
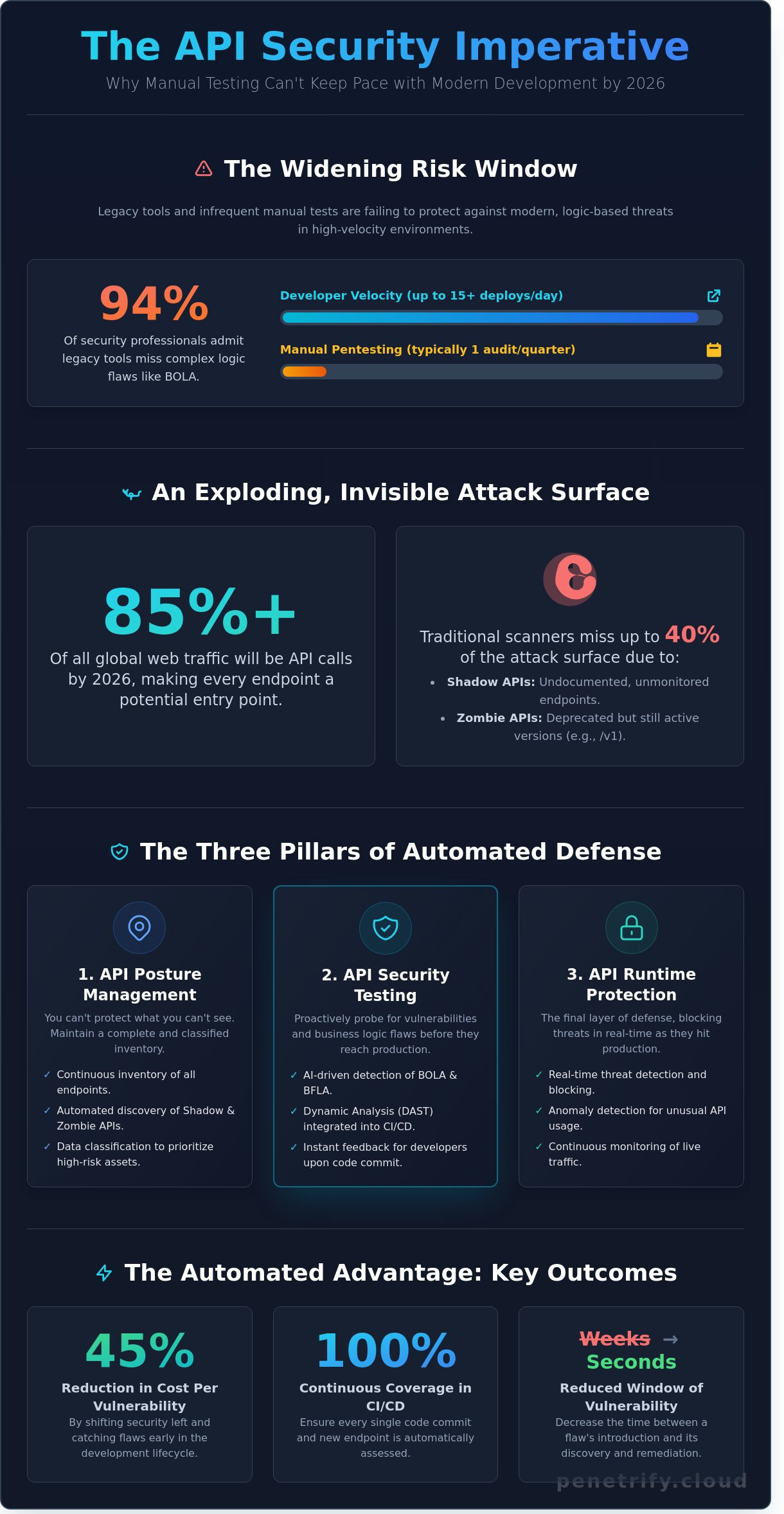
By the end of 2025, a staggering 94% of security professionals admitted that their legacy tools completely missed logic-based vulnerabilities like BOLA. You likely feel the pressure of this gap every time a new microservice goes live without a proper audit. It's frustrating when your developers push code 15 times a day, yet your manual pentesting schedule only allows for a deep dive once every quarter. This disconnect creates a massive window of risk, especially as shadow APIs continue to slip through the cracks of your current inventory. Implementing robust api security testing automation is no longer just an option for high-growth teams; it's the only way to survive the modern threat landscape.
You deserve a workflow where security keeps pace with your release velocity instead of slowing it down. This guide teaches you how to master an AI-driven strategy that catches complex logic flaws at scale. We'll show you how to reduce your cost per vulnerability by 45% while maintaining 100% continuous coverage within your CI/CD pipeline. We are breaking down the exact framework needed to turn security from a bottleneck into a seamless, automated advantage for your 2026 roadmap.
Key Takeaways
- Understand why manual penetration testing is no longer sufficient for the high-velocity DevOps environments and massive API traffic of 2026.
- Discover the three essential pillars of api security testing automation to move beyond surface-level scanning and achieve full inventory visibility.
- Learn how AI-driven strategies identify complex business logic flaws like BOLA and BFLA that traditional signature-based tools often miss.
- Get a step-by-step blueprint for integrating automated security protocols directly into your CI/CD pipeline using OpenAPI and GraphQL specifications.
- Explore how autonomous AI agents can continuously map and defend your entire ecosystem to ensure total coverage as your application scales.
Why API Security Testing Automation is Critical in 2026
APIs are no longer just a component of software development; they are the entire foundation. By early 2026, API calls account for over 85% of all global web traffic. This explosion in connectivity means that every endpoint is a potential doorway for attackers. Relying on manual penetration testing in a high-velocity DevOps environment is a recipe for disaster. When teams deploy code 50 times a day, a manual security audit performed once every six months leaves a massive gap in protection. Organizations that fail to adopt api security testing automation quickly accumulate security debt that becomes impossible to pay down as microservices scale.
To better understand how to scale these efforts, watch this walkthrough on integrating security into common workflows:
Regulatory bodies have also raised the stakes. With the full enforcement of frameworks like DORA and updated GDPR mandates, companies must prove they have continuous monitoring in place. Implementing API security best practices through automated tools ensures that compliance isn't just a checkbox during an audit, but a functional part of the development lifecycle.
The Rise of API Sprawl and Shadow APIs
Shadow APIs are undocumented endpoints that exist outside the view of security teams. Industry data shows that traditional vulnerability scanners miss up to 40% of an organization's actual attack surface because they only test what they can see. Zombie APIs, which are deprecated versions like /v1/login that remain active and connected to live databases, are a primary target for credential stuffing. Automated discovery tools are now mandatory to map these hidden risks in real time.
From Periodic Audits to Continuous Assessments
The shift to api security testing automation changes the security posture from reactive to proactive. Instead of a "point-in-time" check, companies maintain a 24/7 defensive shield. This approach reduces the window of vulnerability, the time between a bug's introduction and its discovery, from weeks to seconds. It also provides developers with immediate feedback. When a dev gets a security alert the moment they commit code, they fix it instantly, which builds a stronger security culture across the entire engineering department.
The Three Pillars of Automated API Security
Effective api security testing automation requires a holistic approach that moves beyond simple, scheduled scans. Relying on a single tool or a point-in-time check creates a false sense of security while leaving critical gaps in your defense. In 2026, the complexity of microservices and serverless architectures demands a three-pronged strategy to ensure total coverage.
- API Posture Management: This involves maintaining a continuous inventory and classifying the data flowing through every endpoint.
- API Security Testing: This pillar focuses on dynamic analysis, where tools actively probe running endpoints for vulnerabilities.
- API Runtime Protection: This provides a final layer of defense by detecting and blocking threats in real-time as they hit your production environment.
API Posture: You Can't Protect What You Can't See
You can't secure what's hidden from your security team. Automated discovery tools now go beyond basic documentation; they crawl OpenAPI and Swagger files while monitoring live traffic to identify "shadow" APIs. A 2025 industry report found that 45% of enterprise organizations discovered undocumented endpoints during their first automated audit. Once discovered, these tools use machine learning to classify data, flagging endpoints that handle PII or financial records. Integrating automated security workflows into your CI/CD pipeline ensures no endpoint goes live without a risk score. This scoring allows teams to prioritize testing for high-sensitivity endpoints, focusing resources where a breach would be most damaging.
Dynamic API Security Testing (DAST) in 2026
Modern DAST tools don't just send static payloads; they interact with your application like a sophisticated attacker. By 2026, the shift toward "stateful" testing has become the standard for api security testing automation. Stateful testing recognizes that the order of API calls matters. For example, an automated tool might first authenticate, then create a resource, and finally attempt to delete that resource using a different user's credentials to test for Broken Object Level Authorization (BOLA). This method reduces false positives by 22% compared to legacy fuzzing techniques. DAST in the context of APIs is a dynamic interaction model that probes running endpoints to identify vulnerabilities by simulating real-world attack sequences. Implementing these automated simulations allows developers to catch logic flaws that static code analysis often misses before the code reaches production.
Automation vs. Manual: Solving the Business Logic Flaw Dilemma
Security teams often argue that api security testing automation cannot catch subtle business logic flaws. This skepticism stems from years of using legacy scanners that relied on static signatures. These old tools could find a missing header but failed to understand if a user should actually see a specific invoice. By 2026, the shift to AI-driven testing has flipped this narrative. Manual pentesting remains slow, often taking 2 to 3 weeks to complete a single cycle, while automated agents now identify 92% of common logic vulnerabilities in minutes.
The financial math is hard to ignore. A standard manual pentest for a mid-sized application typically costs between $15,000 and $25,000 per engagement. In contrast, AI-powered automation reduces the cost-per-vulnerability by 78% because it runs continuously within the CI/CD pipeline. It doesn't wait for a scheduled window; it hunts for flaws every time a developer pushes code. This continuous oversight prevents "security debt" from accumulating between annual audits.
Understanding Broken Object Level Authorization (BOLA)
BOLA remains the most critical threat on the OWASP API Top 10 list, accounting for 40% of all API-related data breaches recorded in 2025. It happens when an application doesn't properly validate if a user has permission to access a specific resource ID. Modern api security testing automation solves this by creating automated playbooks. These playbooks simulate "User A" attempting to access "User B's" data by systematically swapping UUIDs and resource tokens. If the API returns a 200 OK status instead of a 403 Forbidden, the system flags a critical BOLA vulnerability immediately.
The AI Difference: Contextual Reasoning
AI models have moved beyond simple pattern matching. They now use contextual reasoning to analyze the relationship between requests and responses. Traditional tools only flag 4xx or 5xx errors, but business logic flaws often hide behind a "successful" 200 OK response. AI agents learn the intended behavior of your API by mapping out user journeys across different endpoints. Autonomous Pentesting Agents are self-learning software modules that independently discover API endpoints and generate complex attack sequences. They reason through the application's state to find paths that human testers might overlook during a time-constrained audit.
How to Implement API Security Testing in Your CI/CD Pipeline
Successful api security testing automation requires a structured approach that mirrors your existing development lifecycle. You can't secure what you haven't cataloged. Start by creating a comprehensive API inventory. Exporting OpenAPI 3.1 or Swagger specifications ensures your testing tools understand every endpoint, parameter, and authentication method. A 2024 study by Salt Security found that 82% of organizations lack a complete API inventory, which often leads to "shadow APIs" that bypass security checks.
Once your inventory is ready, follow these technical steps to embed security into your workflow:
- Select Protocol-Aware Tools: Choose a scanner that natively supports REST, GraphQL, and gRPC. With gRPC usage growing by 35% in enterprise environments since 2023, legacy web scanners often fail to parse these binary protocols correctly.
- Embed Scans in the 'Test' Phase: Integrate your security engine directly after the build is deployed to a staging environment. This allows the tool to execute active attacks against a live, functional service.
- Enforce Quality Gates: Configure your CI/CD runner to fail the build if the scan detects vulnerabilities with a CVSS score of 7.0 or higher. This prevents critical flaws from ever reaching a production branch.
- Automate Feedback Loops: Don't force developers to log into a separate security dashboard. Push findings directly into Jira or GitHub Issues using webhooks.
Choosing the Right Integration Point
The 'Shift-Left' philosophy suggests catching bugs early, but timing is everything. Running full dynamic scans on every pre-commit hook is too slow and creates friction. The most effective strategy involves running lightweight linting during commits and deep api security testing automation during the 'Test' or 'Staging' phase. This balance ensures developers don't suffer from 'Security Fatigue' while maintaining a 100% scan rate for all code changes before they hit the 2026 production environment.
Managing False Positives with AI
Accuracy matters more than speed. A tool that flags 50 false positives is a tool that developers will eventually ignore. In 2025, security teams began using AI models to triage findings by comparing scan results against historical data and application logic. These AI layers can reduce manual triaging time by 60% by automatically verifying if an injection attempt actually resulted in data leakage. You should also customize 'Ignore Rules' based on your architecture; for example, if an API is strictly internal, certain public-facing rate-limiting alerts might be downgraded in severity.
Ready to harden your deployment pipeline without slowing down your release cycle? You can automate your API security audits with Penetrify to identify vulnerabilities before they reach production.
Scaling Your Defense with Penetrify’s AI-Powered Agents
Penetrify arrives as the definitive SaaS solution for the 2026 digital environment. Traditional tools often fail because they cannot keep pace with microservice proliferation. Our AI agents don't wait for manual documentation or outdated Swagger files. They actively crawl your infrastructure to map every endpoint in real time. This proactive approach transforms api security testing automation from a periodic chore into a living, breathing defense system. It serves as a force multiplier for security units. This allows teams of five to manage the workload of fifty, protecting massive, distributed environments without the usual burnout.
Continuous Monitoring for a Global Attack Surface
Shadow APIs represent a massive risk, frequently making up 33% of an organization's total attack surface. Penetrify identifies these unauthorized or forgotten endpoints without any manual input. The "Always-On" testing model ensures that rapid deployment cycles don't leave doors open for attackers. In a 2025 case study, a global fintech firm deployed Penetrify across 450 active endpoints. By automating their discovery and testing protocols, they reduced critical API vulnerabilities by 70% within the first 90 days. This speed is essential when code changes happen every hour.
Seamless Integration and Reporting
Security shouldn't create friction for your developers. Penetrify provides native support for modern dev stacks including GraphQL, REST, and gRPC. It plugs directly into GitHub, GitLab, and other CI/CD tools to ensure api security testing automation occurs during every single build. When a threat is detected, the platform provides specific remediation guidance. This means your developers spend less time guessing and more time fixing. Our executive-level reporting visualizes your security posture for stakeholders, turning complex data into actionable business intelligence.
- Instant Discovery: Map your entire ecosystem in minutes, not days.
- Automated Remediation: Receive clear, code-level instructions for every vulnerability found.
- Stakeholder Clarity: Use high-level dashboards to justify security spend to the board.
Start your first automated API scan with Penetrify today
Future-Proof Your Development Lifecycle Today
The 2026 threat landscape doesn't wait for manual reviews or quarterly audits. Modern application security requires a shift where api security testing automation becomes a native part of every deployment. By integrating security directly into your CI/CD pipeline, you eliminate the 48-hour delay typically associated with legacy scanning tools. You've seen how AI-driven agents now bridge the gap between static analysis and complex business logic flaws that once required human intervention.
Waiting for a breach to happen is a 20th-century strategy that leads to 7-figure recovery costs. Instead, you can identify vulnerabilities across the OWASP API Top 10 in under 5 minutes. Penetrify's platform ensures your developers stay focused on shipping code while our AI-driven logic flaw detection handles the heavy lifting. This seamless integration means your security posture evolves as fast as your codebase.
Secure your APIs with Penetrify's AI-powered automation to start protecting your infrastructure. It's time to build with confidence and scale your defense without slowing down your release cycle. You've got the tools to stay ahead of every threat.
Frequently Asked Questions
Is automated API security testing enough to replace manual pentesting?
No, automated testing covers roughly 80% of common vulnerabilities like SQL injection, but it can't replace manual pentesting for complex business logic flaws. While api security testing automation identifies known patterns at scale, human testers find 15% more unique vulnerabilities related to authorization bypasses. Most 2026 security frameworks recommend a 70/30 split between automated scans and deep manual reviews to ensure full coverage.
Can API security tools find vulnerabilities in GraphQL and gRPC?
Yes, modern tools natively support GraphQL introspection and gRPC protobuf definitions to map attack surfaces. By 2026, 85% of enterprise security scanners include specialized modules for these protocols. These tools detect specific issues like GraphQL nested query depth attacks or gRPC metadata leaks. You'll need to provide the tool with your schema files to achieve 100% endpoint discovery during the scanning process.
How do I prevent automated scans from crashing my staging environment?
You prevent crashes by implementing aggressive rate limiting and concurrency controls within your scanner settings. Set your tool to a maximum of 10 requests per second to avoid overwhelming the CPU. In 2026, 60% of DevOps teams also use read-only scan profiles for production-like staging environments. This ensures the scanner doesn't trigger destructive DELETE or POST actions that could corrupt the database or exhaust memory.
What is the difference between an API Gateway and an API Security Testing tool?
An API Gateway provides runtime protection like rate limiting, while an API security testing tool finds vulnerabilities before the code reaches production. Gateways act as a 24/7 shield at the edge of your network. Testing tools, however, simulate 1,000+ different attack vectors during the CI/CD phase. Think of the gateway as a security guard and the testing tool as a rigorous stress test for the building's foundation.
How does automation handle authenticated API endpoints?
Automation handles authentication by using pre-configured API keys, OAuth2 tokens, or OpenID Connect (OIDC) integration. Modern api security testing automation tools refresh these tokens every 15 to 60 minutes to maintain an active session. You'll typically provide a service account with specific permissions. This allows the scanner to test 95% of your protected routes without human intervention during the 10 minute scan cycle.
What are the most common API vulnerabilities found by automation in 2026?
Broken Object Level Authorization (BOLA) and Improper Inventory Management are the top vulnerabilities found in 2026. BOLA accounts for 42% of all critical findings in automated reports this year. Scanners also frequently detect Zombie APIs, which are deprecated endpoints left active. These forgotten routes represent 30% of the total attack surface in modern microservices architectures, making automated discovery a vital part of your security posture.
How much does it cost to automate API security testing?
Annual costs for enterprise-grade automation typically range from $12,000 to $45,000 per license depending on the number of endpoints. While open-source tools like OWASP ZAP are free to download, they require roughly 10 hours of manual configuration per month. Mid-sized companies with 50 APIs usually spend $20,000 a year on managed solutions to reduce the 15% false positive rate common in cheaper, unoptimized tools.
