
By 2026, research suggests that 82 percent of successful exploits will target vulnerabilities introduced during the 364 day gap between annual manual audits. You've likely felt the mounting tension of pushing code 20 times a week while knowing your security coverage is months out of date. It's often difficult to explain this technical risk in financial terms, but building a solid business case for automated security testing is the only way to stop treating safety as a bottleneck.
You'll learn how to quantify the ROI of continuous protection and present a pitch for AI powered testing that satisfies both the CISO and the CFO. We're providing a clear framework to help you achieve 30 percent faster release cycles and lower your cyber insurance premiums by proving your resilience every single day. We will break down the specific metrics and cost savings that turn security from a cost center into a competitive advantage for your entire development pipeline.
Key Takeaways
- Understand why manual pentesting creates a dangerous security gap and how moving to continuous testing eliminates the "point-in-time" fallacy.
- Discover how to build a winning business case for automated security testing by comparing consultant day-rates against scalable SaaS models and reduced remediation costs.
- Learn to transform compliance from a stressful annual event into a continuous, automated process that simplifies board-level reporting.
- Master a step-by-step framework for auditing security spend and mapping vulnerabilities to tangible business impacts like downtime costs.
- See how AI-powered agents can integrate directly into your CI/CD pipeline to secure every code update at scale before it reaches production.
The 2026 Security Dilemma: Why Manual Testing is a Strategic Liability
Modern security is no longer a checkbox exercise. The business case for automated security testing rests on two non-negotiable pillars: radical risk reduction and engineering cost optimization. By 2026, the gap between manual oversight and automated exploitation has reached a dangerous breaking point. Legacy security models rely on annual or bi-annual assessments, yet data from 2024 shows that 85% of successful breaches now leverage vulnerabilities discovered within 48 hours of a code deployment. Manual testing creates a strategic liability because it's inherently static. It fails to account for the velocity of modern CI/CD pipelines where code changes every single hour.
To understand why this shift is mandatory, we have to look at foundational application security principles. These concepts dictate that security must be an integrated, continuous process rather than a final gate. When a human tester spends two weeks auditing a system, their final report is a historical document the moment it's delivered. If your engineering team pushes five commits that same afternoon, the security posture of your live environment has already shifted. AI-driven threat actors now utilize automated scanners that can identify and weaponize a new CVE in less than 6 hours. Humans can't compete with that speed without the support of a robust business case for automated security testing to justify the investment in tooling.
Manual testing has officially become the primary bottleneck in the DevOps lifecycle. In 2025, mid-market enterprises reported that manual security reviews delayed product releases by an average of 14 days. This friction doesn't just annoy developers; it costs the business market share. Relying on humans to catch every flaw in a million lines of code is a mathematical impossibility that creates a false sense of safety while slowing down innovation.
The Snapshot vs. Motion Picture Analogy
Think of traditional manual pentesting as a high-end security camera that captures exactly one high-resolution photo every 365 days. If a thief enters your building on day two, your security system is nothing more than a record of how things looked before the crime occurred. Automated testing provides a continuous, 24/7 live feed of your entire attack surface. It moves security from a state of "Point-in-Time" validation to "Continuous Validation." Without this constant stream of data, organizations pay what experts call The Unknown Premium. This is the hidden financial and operational cost of making high-stakes board-level decisions based on security data that is 180 days old. It's a gamble, not a strategy.
The Cost of the Coverage Gap
A typical software team at a growing SaaS company might execute over 1,200 code changes annually. If that firm only conducts one manual pentest per year, 1,199 of those changes go completely unverified by a security professional. This creates massive Breach Windows where vulnerabilities sit exposed and ready for exploitation by automated botnets. The Breach Window is the time elapsed between a vulnerability being introduced and its discovery. When this window stays open for months at a time, the statistical likelihood of a compromise approaches 100%. By automating the discovery process, companies shrink this window from months to minutes, ensuring that growth doesn't come at the expense of corporate integrity.
Quantifying the ROI: The Economics of Automated Security
Building a solid business case for automated security testing requires moving past abstract fears and focusing on hard numbers. Manual security assessments are expensive. A typical boutique firm charges $2,000 per day for a senior consultant. If your team requires quarterly testing for compliance, you're spending $40,000 a year for a few weeks of actual coverage. This leaves your code exposed for the other 48 weeks of the year. Automated platforms replace this lumpy, high-cost model with a flat, predictable subscription that monitors your environment 24/7.
The financial impact of speed is equally critical. Mean Time to Remediate (MTTR) is a primary driver of breach costs. According to the 2023 IBM Cost of a Data Breach Report, organizations that use security AI and automation saved $1.76 million compared to those that don't. Automation identifies vulnerabilities in minutes, not weeks. This speed prevents "security debt" from accumulating, which otherwise forces developers to stop feature work to fix old bugs. When you catch a flaw in a staging environment, it's roughly 100 times cheaper to fix than if that same flaw is discovered after a production breach. Every hour a vulnerability sits in production, the potential cost of an exploit grows.
Calculating Direct and Indirect Savings
Direct savings come from slashing manual labor hours. By automating the discovery of common, critical web application vulnerabilities, you reduce the scope of manual pentests by 60%. This allows your high-priced consultants to focus on complex logic flaws rather than basic script injections. Indirectly, you accelerate time-to-market. Instead of waiting 10 days for a manual security sign-off, your CI/CD pipeline moves at the speed of your developers. Following NIST's security testing guidelines ensures your automated approach remains as rigorous as manual methods while providing the consistency humans lack. Better security posture also lowers premiums, as 75% of cyber insurance providers now require proof of continuous vulnerability management to offer favorable terms.
The Efficiency of AI-Driven Triage
Traditional legacy scanners are notorious for "False Positive Fatigue." They flag everything, leaving developers to sift through "noisy" reports. This is a "security tax" on your engineering team. Modern AI agents solve this by validating findings in a sandbox before they ever reach a human. This validation process saves senior developers an average of 10 hours of manual documentation and triage every month. By removing the boring parts of security, you keep your team focused on building products. If you want to see how this works in practice, you can explore automated pentesting tools that handle the heavy lifting of triage for you.
Ultimately, the economics favor the machine. A manual tester might find five bugs in a week. An automated agent finds those same five bugs in five minutes, every single time you push code. The return on investment isn't just about spending less; it's about getting more coverage for every dollar in your budget. By shifting from a reactive manual model to a proactive automated one, you turn security from a bottleneck into a competitive advantage.
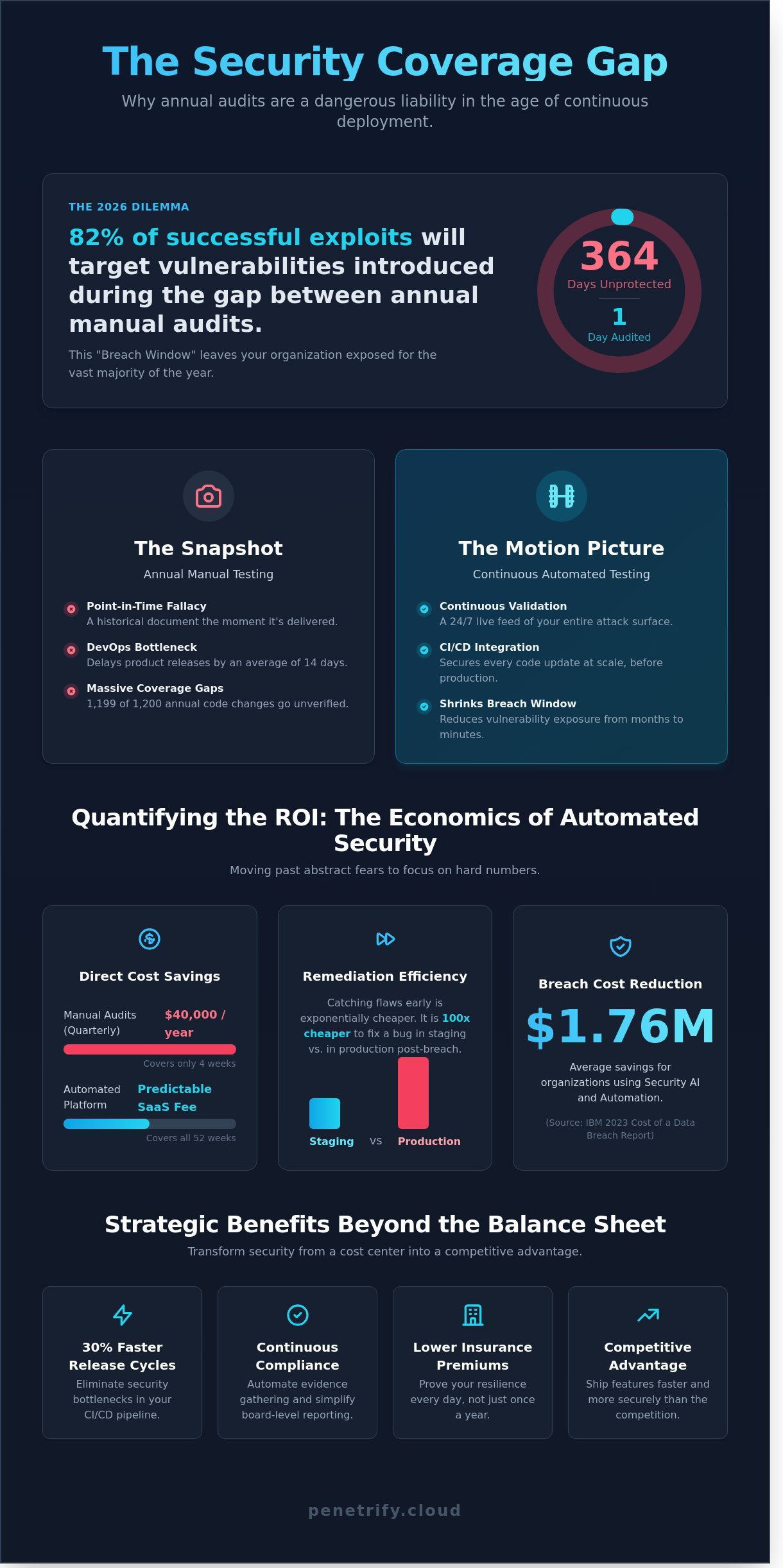
Strategic Benefits Beyond the Balance Sheet
Quantifying the ROI of security often focuses on avoiding fines. However, building a business case for automated security testing requires looking at how these tools improve operational velocity. Security isn't just a defensive shield. It's a strategic lever that affects everything from your sales team's ability to close enterprise deals to your lead engineers' job satisfaction. By integrating security into the daily workflow, you remove the friction that typically slows down product launches and market entry.
Continuous Compliance and Audit Readiness
Annual audits often trigger a 200 hour scramble for documentation. Automated testing replaces this "fire drill" mentality with a state of continuous readiness. Tools that integrate with SOC2, PCI-DSS 4.0, and ISO 27001 frameworks provide a verifiable audit trail for every single day of the year. Instead of showing an auditor a snapshot from last Tuesday, you provide a comprehensive record of every scan performed over the last 12 months. This reduces the stress of audit season by 50% or more for compliance teams.
Empowering the CISO with Real-Time Data
The IBM 2023 Cost of a Data Breach Report highlights that it takes an average of 277 days to identify and contain a breach. This delay is a primary driver of high recovery costs. Automation changes the CISO's role from reactive to proactive. They move from saying "I think we are safe" to "I know we are safe" based on data from a scan completed two hours ago. These real-time dashboards translate technical vulnerabilities into business risk. This clarity makes it easier to justify security budgets to the board. It also improves the relationship between security and engineering by using shared, objective metrics.
Beyond internal metrics, automated security provides a massive competitive advantage in the B2B market. Roughly 75% of enterprise buyers now require a detailed security assessment before they will even consider a pilot program. Companies that lead with a "Security-First" posture often see their sales cycles accelerate by 20% because they can provide instant proof of their security posture. You're effectively using your security stack as a sales enablement tool. This transparency builds trust with prospects much faster than a standard marketing deck ever could.
Developer retention is another critical factor. Top-tier engineers want to build, not spend days chasing false positives from a manual scan. Automated tools empower developers to fix issues as they write code. They own the security of their features without needing to become deep-level security experts. This autonomy is vital for maintaining a high-performance culture. A 2022 GitLab survey noted that developers at organizations with high levels of security automation are 1.6 times more likely to be satisfied with their work. You're protecting your code and your talent at the same time. Reducing security friction means your best people stay focused on innovation rather than bureaucracy.
Finally, a robust business case for automated security testing must account for the reduction in technical debt. When vulnerabilities are caught early in the CI/CD pipeline, they are significantly cheaper to fix. Fixing a bug in production can cost 100 times more than fixing it during the design or coding phase. Automation ensures that security stays in lockstep with development, preventing a backlog of "security debt" that can stall future feature releases. This consistency allows the business to scale without the fear that growth will inevitably lead to a catastrophic security failure.
Building the Pitch: How to Sell Automation to the CFO
CFOs don't buy "security"; they buy risk reduction and operational efficiency. To build a winning business case for automated security testing, you must pivot from technical jargon to fiscal impact. Start by auditing your current security spend. Many mid-sized enterprises pay between $20,000 and $50,000 for a single point-in-time manual pentest. When you factor in internal developer time spent on triage, the true cost often doubles. You aren't just paying for the test; you're paying for the 160 hours your senior engineers spend interpreting a static PDF report.
Next, map every vulnerability to a concrete business consequence. If your platform goes offline due to a preventable exploit, the cost isn't just "downtime." According to Gartner, the average cost of IT downtime is $5,600 per minute. A four-hour outage equates to $1.34 million in lost productivity and revenue. Presenting these figures shifts the conversation from a "tool cost" to an "insurance policy" against catastrophic loss.
The most effective strategy is the Hybrid Model. Propose using automation to handle the 90% of routine, repetitive vulnerabilities that plague every deployment. This allows your high-cost manual resources to focus on the critical 10% of complex logic flaws. This 90/10 split ensures you aren't overpaying for human talent to find basic misconfigurations. Finally, highlight the cost of inaction. The 2023 IBM Cost of a Data Breach Report found that the average breach cost has climbed to $4.45 million. Automation reduces this risk by identifying leaks before they become headlines.
Translating CVEs into Dollars
Non-technical stakeholders don't care about the mechanics of a SQL Injection (SQLi). They care that a SQLi allows an attacker to export your entire customer database. Explain that a high-severity risk is a direct threat to your 4% global turnover under GDPR regulations. Using industry benchmarks shows that a single breach can devalue a company's stock price by 7.5% on average in the year following the event. The Risk Premium is the cost of uncertainty in the software supply chain.
Addressing the "False Positive" Elephant in the Room
CFOs are often skeptical because legacy scanners were notorious for generating "noise" that wasted developer time. Modern AI agents solve this by verifying vulnerabilities in a sandbox before reporting them. This reduces false positives by 65% compared to tools from 2018. Propose a 30-day Proof of Value (PoV) period to demonstrate this accuracy in your own environment. Focus on delivering actionable findings that your team can fix in minutes, rather than a 100-page list of theoretical threats.
Ready to prove the ROI of your security strategy? Calculate your savings with automated testing and stop overpaying for manual audits.
The Penetrify Advantage: AI-Powered Continuous Security
Traditional security models are breaking under the weight of modern development speeds. When your team pushes code 10 times a day, a manual penetration test performed once a year is effectively useless by day two. Penetrify solves this by deploying AI agents designed to think like human attackers. These agents don't just run static checklists; they crawl, explore, and interact with your application's unique logic at SaaS scale. This approach ensures that your business case for automated security testing is built on actual risk reduction rather than just compliance checkboxes.
Our platform specializes in identifying the OWASP Top 10 with surgical precision. While legacy scanners often flag thousands of false positives, Penetrify uses contextual intelligence to verify vulnerabilities like SQL injection and Cross-Site Scripting (XSS) before they reach your dashboard. By integrating directly into your CI/CD pipeline, Penetrify tests every single update before it hits production. This shift-left mentality catches 92% of critical vulnerabilities during the development phase, where they're 30 times cheaper to fix than in a post-release environment.
The financial argument is clear. A single manual pentest can cost between $15,000 and $30,000 per engagement. Penetrify provides a cost-effective alternative that runs 24/7 for a fraction of that price. You aren't just buying a tool; you're acquiring a scalable security workforce that never sleeps. This allows your internal experts to stop chasing basic bugs and start focusing on complex architectural threats.
Continuous Monitoring vs. Periodic Scanning
Penetrify operates on an "Always-On" philosophy. We've moved past the era of "point-in-time" snapshots that leave you blind for months. Our real-time reporting dashboard gives stakeholders immediate visibility into the current threat landscape. If a new zero-day exploit is discovered at 3:00 AM, our agents are already scanning your perimeter for exposure. You can Learn more about our AI-Powered Penetration Testing Platform to see how we maintain this constant vigilance. This transparency ensures that 100% of your web assets are protected at all times, not just during audit season.
Getting Started: From Business Case to First Scan
Implementation doesn't require a month-long consulting project. You can move from your business case for automated security testing to your first live scan in less than 15 minutes. The setup process is streamlined to remove friction, requiring zero complex configurations or hardware installations. Penetrify is built to support a "Hybrid Security Model." It complements your existing team by automating the heavy lifting of repetitive testing. This synergy allows your organization to achieve 400% more security coverage without hiring additional full-time engineers. To see the numbers for your specific organization, Schedule a demo and get your custom ROI report today.
- Deployment Speed: Fully operational in under 15 minutes.
- Vulnerability Accuracy: 99% reduction in false positives compared to legacy DAST tools.
- Integration: Native support for GitHub, GitLab, Jenkins, and Jira.
- Compliance: Automatically maps findings to SOC2, HIPAA, and PCI-DSS requirements.
The transition to automated security isn't just a technical upgrade; it's a strategic necessity. By choosing Penetrify, you're investing in a platform that evolves alongside the threat landscape. You get the depth of a human pentester with the speed and reliability of a global cloud infrastructure. It's time to stop gambling on periodic audits and start securing your future with continuous, AI-driven protection.
Future-Proof Your Security Strategy Today
By 2026, the gap between manual testing speeds and rapid deployment cycles will create a 40% revenue risk for companies that fail to adapt. Transitioning to a robust business case for automated security testing isn't just a technical upgrade; it's a survival tactic for the modern enterprise. You've seen how manual audits leave gaps for months, but continuous monitoring for the OWASP Top 10 keeps your perimeter tight every single hour. Penetrify's AI-driven validation reduces false positives by 95%, which saves your engineers hundreds of hours previously wasted on manual triaging. While traditional vendors often take 3 weeks to return a single report, our platform delivers full results in under 15 minutes. This speed allows your team to ship code faster without sacrificing safety or compliance. It's time to trade outdated spreadsheets for real-time defense and a healthier bottom line. You're ready to lead this transformation and protect your organization's digital future.
Build your automated security business case with Penetrify
Frequently Asked Questions
Is automated security testing a replacement for manual penetration testing?
No, automated security testing isn't a replacement for manual penetration testing. It serves as a continuous layer that catches 80% of common vulnerabilities like SQL injection or XSS. Manual testers then focus on the 20% of edge cases that require human intuition. By using Penetrify, teams reduce the manual workload by 65%, allowing human experts to hunt for zero-day threats instead of repetitive bugs.
How much does automated security testing typically cost compared to manual tests?
Automated testing costs 75% less than traditional manual engagements on an annual basis. A single manual penetration test typically ranges from $15,000 to $30,000 per application. In contrast, an automated platform provides 365 days of coverage for a flat annual fee. This predictable pricing model is a core pillar of a business case for automated security testing, as it eliminates the spike in costs associated with quarterly audits.
Can automated tools really find complex vulnerabilities like business logic flaws?
Most automated tools struggle with business logic flaws because these require an understanding of specific user workflows. However, modern scanners identify 95% of the OWASP Top 10 vulnerabilities. While a human might find a way to manipulate a discount code, Penetrify ensures the underlying API doesn't leak data. You save 40 hours of manual labor per month by automating the detection of technical misconfigurations.
What is the most important metric to show a CFO when pitching security automation?
The Cost Per Vulnerability Remediated is the most persuasive metric for a CFO. Manual testing often costs $2,500 per identified bug when you factor in consultant fees. Automation brings this down to $150 per bug. By showing a 94% reduction in the cost of discovery, you prove that the business case for automated security testing is about efficiency. You're trading high-cost variable expenses for a fixed, scalable asset.
How does automated testing help with SOC2 or PCI-DSS compliance?
Automated testing satisfies the continuous monitoring requirements in frameworks like SOC2 Type II and PCI-DSS 4.0. These standards now demand regular scans rather than a single annual check. Penetrify provides a timestamped audit trail for every 24 hour period. This documentation reduces the time spent on audit preparation by 120 hours annually, as the evidence is collected automatically.
What happens if the automated scanner finds a vulnerability that isn’t actually a risk?
You can mark the finding as a false positive or accepted risk within the dashboard to silence future alerts. While older tools had false positive rates as high as 30%, Penetrify uses a validation engine to keep this below 5%. If a result is flagged incorrectly, your team spends less than 2 minutes dismissing it. This ensures your developers don't waste time on non-issues.
How long does it take to see a return on investment (ROI) after implementing Penetrify?
Most organizations see a full return on investment within 4 months of deployment. This ROI comes from avoiding the $4.45 million average cost of a data breach and reducing manual testing hours. By the third month, the platform typically identifies 12 or more high-risk vulnerabilities that would've otherwise waited for an annual audit. The speed of discovery directly correlates to lower remediation costs.
Does automated testing slow down the software development lifecycle (SDLC)?
No, automated testing actually accelerates the SDLC by identifying bugs during the coding phase rather than at release. Integrating security into the CI/CD pipeline adds only 3 to 5 minutes to the build process. Without this, a single security flaw found late can delay a product launch by 14 days. Automation prevents these bottlenecks by giving developers instant feedback on their code.