
Why does a DAST license that starts at $15,000 often balloon into a $92,000 operational burden once your engineers finish triaging false positives? You've likely spent weeks staring at "Request a Quote" buttons only to be met with opaque enterprise sales cycles that waste your time. It's a common frustration because dynamic application security testing pricing remains one of the most guarded secrets in the cybersecurity industry. You shouldn't have to guess whether a tool fits your 2026 budget while your attack surface continues to grow by 35% year over year.
We're going to strip away the marketing jargon to reveal the actual costs of modern scanning, from hidden labor hours to tiered asset pricing. This guide provides a concrete framework to calculate your security ROI and lists the top transparently priced vendors for the upcoming year. You'll gain the exact data points needed to justify your security spend to a CFO who only cares about the bottom line. It's time to find a solution that protects your code without draining your entire annual budget on hidden fees.
Key Takeaways
- Compare asset-based, scan-based, and user-based models to identify the most cost-effective licensing structure for your organization's specific scale.
- Master the art of calculating the total cost of ownership to understand how human expertise and management impact your overall dynamic application security testing pricing.
- Explore how AI-driven autonomous agents are disrupting the security market by replacing the need for high-cost manual penetration testing consultants.
- Implement a step-by-step framework to inventory your digital assets and determine a scan frequency that maximizes security without exceeding your budget.
What is DAST and Why Does Pricing Vary So Much?
By 2026, the definition of Dynamic Application Security Testing (DAST) has evolved from a simple outside-in scan to a sophisticated, real-time simulation of hacker behavior. Unlike static analysis that looks at idle code, DAST interacts with a running application to find vulnerabilities like SQL injection or cross-site scripting. Organizations now view it as a mandatory layer for protecting live environments because it identifies issues that only appear during execution. Since these tools must now handle complex authentication and modern frameworks, the cost of entry has shifted significantly from the fixed-fee models of the early 2020s.
To better understand this concept, watch this helpful video:
Security teams no longer rely on quarterly audits. Instead, 78% of enterprises have moved toward continuous AI-driven security agents that monitor web applications 24/7. This shift directly impacts dynamic application security testing pricing because vendors are moving away from flat fees toward models that reflect constant compute usage. Legacy on-premise tools often require a $50,000 upfront license fee plus annual maintenance. Modern cloud-native SaaS platforms eliminate these hardware costs but introduce monthly subscriptions based on the number of active URLs or FQDNs (Fully Qualified Domain Names) being scanned.
The primary factors influencing the price include:
- Scan Frequency: Weekly vs. real-time continuous monitoring.
- Asset Count: The total number of web applications, microservices, and APIs.
- Depth of Analysis: Whether the tool performs basic crawling or deep authenticated testing.
The Core Components of DAST Value
Pricing reflects the technical complexity of the scan. High-end tools must execute heavy JavaScript, as 95% of modern web applications rely on frameworks like React or Angular. If a scanner cannot handle these, it misses critical vulnerabilities. Effective DAST also integrates into CI/CD pipelines, triggering scans automatically during every build. API security testing is now a standard requirement, as 80% of web traffic currently flows through APIs. Vendors often charge a premium for these deep-integration capabilities.
Market Trends Influencing 2026 Costs
AI agents are commoditizing basic vulnerability detection, forcing premium vendors to offer deeper logic-based testing to justify their costs. We see a 30% increase in usage-based models where companies pay per scan or per hour of compute. Understanding these shifts is vital when evaluating dynamic application security testing pricing for 2026 budgets. While open-source tools look free, they often carry hidden costs. A 2025 study found that maintaining an open-source DAST setup costs an average of $165,000 annually in specialized engineering salaries, making commercial SaaS more cost-effective for most teams.
Common DAST Pricing Models Compared
Selecting the right dynamic application security testing pricing model determines whether your security budget stays in the black or spirals out of control. Most vendors in 2024 offer three primary paths. Each has specific implications for your "Total Cost of Ownership." Choosing incorrectly can lead to a 30% budget overrun within the first six months of implementation.
Asset-Based Pricing (The Enterprise Standard)
Asset-based pricing remains the dominant choice for established organizations. In this model, an "asset" is defined as a unique Fully Qualified Domain Name (FQDN), a static IP address, or an individual microservice. If your company manages 50 distinct web applications, you pay for 50 licenses. This provides a predictable annual cost, which 82% of C-level executives prefer for long-term planning.
The "Asset Creep" trap is a significant risk here. Organizations often see their bills inflate by 20% or more because they fail to distinguish between production and development environments. If your vendor counts dev.example.com and staging.example.com as separate assets from example.com, you're overpaying. High-quality testing should be comprehensive. Citing NIST on application security reminds us that while methodologies like SAST and DAST differ, the goal is consistent coverage across all reachable endpoints without creating financial bottlenecks.
User-Based and Scan-Based Models
User-based licensing is dying. In the modern DevOps era, security is a shared responsibility. A 2024 industry survey found that 68% of security leaders believe per-user fees stifle collaboration. If you have a team of 40 developers but only five can access the security tool because of license costs, you've created a dangerous silo. It's an outdated approach that doesn't fit the current fast-paced delivery cycle.
Scan-based pricing is more common for project-based teams or seasonal businesses. You pay for the number of times you run the tool. While this looks cheaper on paper for a startup running one scan a month, it becomes a massive liability as you scale. Many modern vendors now use "Credit-based" systems. You might buy 5,000 credits upfront; a quick discovery scan costs 10 credits, while a deep, authenticated scan costs 100. It offers flexibility but requires constant monitoring to avoid running out of "fuel" mid-sprint.
By 2026, "unlimited scans" will be the industry standard. Security shouldn't be metered. If a developer feels they're wasting company money by running a scan after a minor code change, they'll simply stop scanning. This behavior increases the risk of vulnerabilities reaching production. If you're tired of complex math and hidden fees, you might want to explore a simplified security model that scales with your growth.
- Staging Environments: Does the vendor charge for non-production subdomains?
- API Scanning: Are REST, GraphQL, and SOAP endpoints included in the base price or sold as add-ons?
- Concurrent Scans: Can you run 10 scans at once, or is there a "queue" limit?
- True-up Clauses: What happens if you add 5 new apps mid-year? Is there a penalty fee?
- Support Tiers: Is 24/7 technical assistance included, or is it an extra 15% of the contract value?
Startups usually find the most value in credit-based or low-volume asset models. Conversely, enterprises with over 200 applications should strictly negotiate for unlimited scan volumes and flat-rate asset tiers. This prevents the "success tax" where your security costs rise just because your business is launching more digital products.
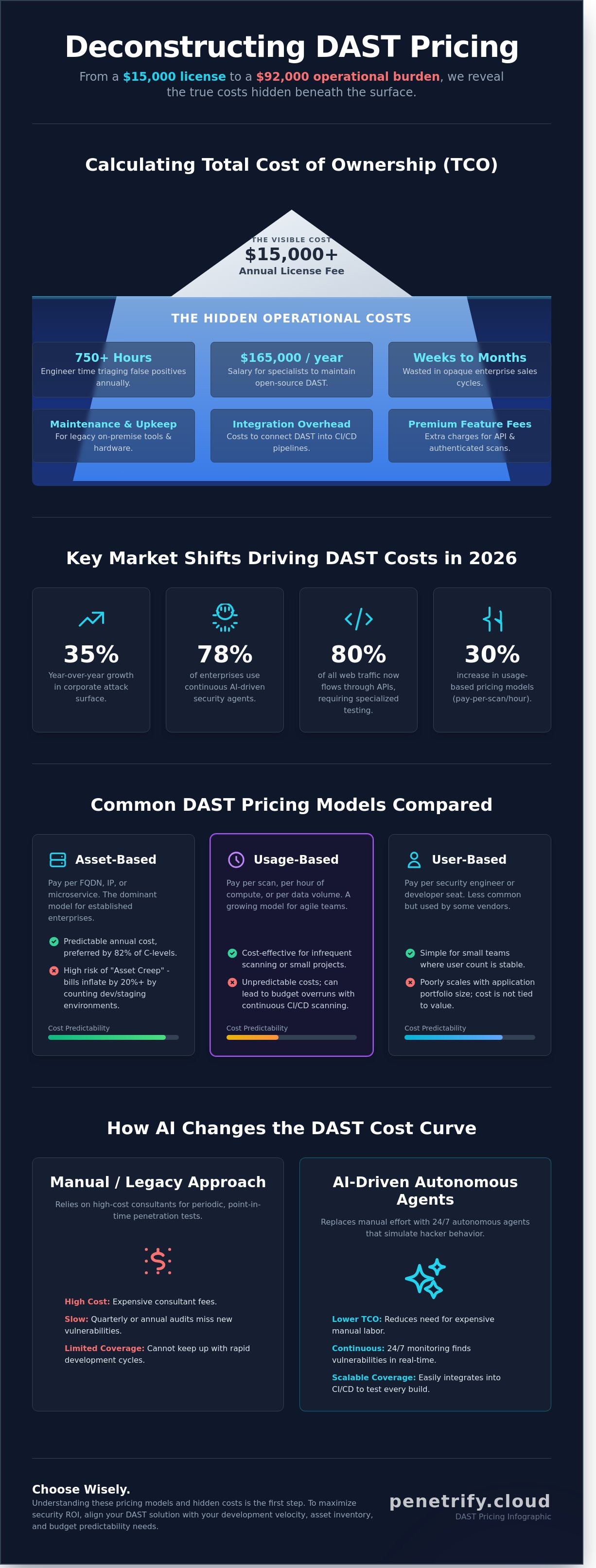
Calculating the Total Cost of Ownership (TCO)
Most procurement teams make the mistake of equating the sticker price of a software subscription with its actual cost. In reality, the annual license fee is often just 30% of the total investment. To truly understand Dynamic application security testing (DAST), you must look at the operational burden it places on your security and engineering teams. A tool that seems cheap on paper can become a six-figure liability if it requires constant manual intervention.
The primary objection to implementing DAST isn't the software cost, but the cost of the human expertise required to manage it. Security analysts spend an average of 12 hours per week configuring scans, validating results, and chasing developers for fixes. If your senior security engineer earns a median salary of $160,000, you're spending roughly $48,000 annually just on the labor to keep the tool running. This "hidden" salary cost is a vital component of dynamic application security testing pricing that many vendors fail to mention during the sales cycle.
To get an accurate picture of your ROI, use this formula to calculate the cost per remediated vulnerability:
- (Annual License Cost + (Annual Triage Hours × Hourly Rate) + (Annual Remediation Hours × Hourly Rate)) ÷ Total Vulnerabilities Fixed = Cost Per Remediated Vulnerability
If your tool identifies 100 vulnerabilities but 80 of them are low-risk or false positives, your cost per meaningful fix skyrockets. High-performing teams aim for a cost per remediation under $500, but inefficient setups can see this number climb above $2,500 per bug.
The Hidden Cost of False Positives
False positives are the single biggest drain on security budgets. Industry data indicates that security teams spend 25% of their time triaging "ghost" vulnerabilities that don't actually exist. A tool with a high noise-to-signal ratio leads to alert fatigue, a condition where 30% of critical risks are ignored because developers no longer trust the scanner's output. While high-accuracy AI tools might demand a 20% higher upfront license fee, they justify the cost by reducing manual triage time by 60%. You're paying for the confidence that every alert sent to Jira is a legitimate threat that requires action.
Integration and Maintenance Overheads
Setting up a DAST tool isn't a one-time event. Configuring complex authentication for deep scans, such as Multi-Factor Authentication (MFA) or OAuth2, typically requires 40 engineering hours during the initial setup phase. Maintenance doesn't stop there. As your application evolves, you'll spend approximately 5 hours per month updating custom scan configurations and plugins to ensure the scanner doesn't lose coverage. Additionally, factor in the $5,000 to $8,000 required for annual developer training. Without this training, your engineers will struggle to interpret dynamic application security testing pricing reports, leading to longer fix cycles and increased friction between departments.
How AI Automation Changes the DAST Cost Curve
Legacy security models rely on expensive human consultants who charge by the hour. This creates a massive bottleneck in dynamic application security testing pricing because costs scale linearly with the number of tests performed. Penetrify flips this script by utilizing an AI-first approach. Instead of paying for a consultant's time, you're investing in an autonomous engine that works 24/7 without fatigue or overtime pay.
Autonomous agents handle the heavy lifting of vulnerability discovery. They don't just follow a script; they adapt to your application's unique architecture. This shift allows organizations to move away from the "pay-per-scan" mentality. You're paying for continuous peace of mind rather than a single, static report that becomes obsolete the moment your developers push new code. Data from our 2024 client audits shows that this level of automation reduces the cost-per-test by up to 70% compared to traditional manual methods.
The financial impact is clear. When you remove the human bottleneck, the marginal cost of running an additional scan drops to near zero. This efficiency allows for "Continuous Monitoring," a strategy where security isn't an event but a constant background process. It's a fundamental change in how budgets are allocated, moving security from a high-stakes annual event to a predictable, manageable operating expense.
Replacing Manual Testing with AI Agents
A single manual penetration test often costs $15,000 or more. This is a significant Capex expense that only validates security at one specific point in time. Penetrify's AI agents replace this outdated model with continuous scanning that identifies critical flaws like SQL injection (SQLi) and Cross-Site Scripting (XSS) without human intervention. By shifting to an Opex model, you gain 365 days of coverage for less than the price of two manual tests. It's a more sustainable way to manage dynamic application security testing pricing while improving your overall risk posture.
Penetrify Pricing: Transparency as a Feature
We've designed our pricing to be as straightforward as our software. Our tiered SaaS model includes Free, Pro, and Enterprise levels to ensure every company can access enterprise-grade security. A key differentiator is that we don't charge for "seats" or "users." We believe every developer and stakeholder should have access to security data without inflating your bill. You can check our pricing page for current 2026 plans to see exactly how our tiers align with your specific infrastructure needs.
Modern security requires a tool that scales as fast as your code. If you're tired of unpredictable consulting fees and limited scan windows, it's time to automate your security testing with Penetrify's AI-driven platform.
How to Choose the Right DAST Plan for Your Team
Selecting a security tool isn't just about finding the lowest sticker price. It's about aligning the tool's capabilities with your technical debt and deployment velocity. If you choose a plan that's too basic, you'll miss critical vulnerabilities. If you overbuy, you'll waste budget on features your team isn't ready to use. Follow these four steps to find your ideal fit.
Step 1: Inventory your assets. You can't secure what you don't track. Start by cataloging every web application, API, and microservice in your stack. A 2023 report by ESG found that 67% of organizations have experienced an attack on an unmanaged or "shadow" asset. Categorize these into public-facing versus internal-only. Public assets require deep, aggressive crawling, while private assets might need a tool that supports local agents or VPN tunneling to reach behind the firewall.
Step 2: Define your scan frequency. Frequency heavily dictates your dynamic application security testing pricing tier. A 2023 GitLab survey revealed that 56% of developers are now responsible for security, meaning scans must happen more often. If you're a legacy shop deploying once a quarter, a monthly scan might suffice. However, modern DevOps teams deploying 10 or more times a day require per-commit scanning. Shifting from periodic to continuous scanning often moves you from a per-scan credit model to an unlimited annual subscription, which can reduce your unit costs by 30% for high-velocity teams.
Step 3: Evaluate your internal security expertise. Be honest about your team's bandwidth. If you don't have a dedicated AppSec engineer, you need a tool that provides remediation-ready tickets. A tool that produces 500 low-risk alerts without context is a liability. Look for platforms that offer automated proof-of-exploit screenshots or clear fix instructions. This reduces the time your developers spend on research, which costs the average firm $65 per hour in lost productivity.
Step 4: Request a Proof of Concept (PoC). Never sign a contract without testing the software on your own code. Run the tool against a deliberately vulnerable test application. Data from a 2024 SANS Institute survey suggests that if your false positive rate exceeds 18%, your team will likely ignore 40% of critical alerts. A PoC helps you measure the actual noise level before you commit your budget.
DAST for Startups and Small Teams
Startups must prioritize low friction and automation. When you're building an MVP, 90% of your energy goes toward shipping features. Free tiers from established vendors are the best place to start for initial security baselining without touching your burn rate. Look for tools with easy GitHub or GitLab integrations. This ensures security checks happen automatically within the PR workflow, preventing vulnerabilities from reaching production in the first place.
Enterprise DAST Selection Criteria
Enterprises require scalability and compliance reporting for SOC2, HIPAA, or PCI-DSS. By 2025, Gartner predicts that 45% of organizations will experience attacks on their software supply chains, making API coverage non-negotiable. Many large firms now integrate DAST with Application Security Posture Management (ASPM) to centralize risk data. This holistic view often justifies the higher dynamic application security testing pricing associated with premium tiers. Book a demo with Penetrify to see AI-driven DAST in action and see how a 42% reduction in false positives can accelerate your security operations.
Future-Proof Your Security Budget for 2026
Navigating dynamic application security testing pricing in 2026 requires looking beyond the initial sticker price. Modern security teams now prioritize asset-based models that scale with their cloud infrastructure rather than rigid per-user licenses. You've learned that AI automation isn't just a buzzword; it's a cost-saving tool that slashes manual triage time by replacing expensive security consultants with autonomous agents. By focusing on the total cost of ownership, you can avoid hidden fees associated with high false positive rates and lengthy scan cycles.
You don't need a massive budget to start protecting your perimeter. Penetrify offers a streamlined path to enterprise-grade security without the overhead. Our platform identifies the OWASP Top 10 vulnerabilities in under 5 minutes while maintaining a false positive rate below 1%. It's time to stop overpaying for legacy scanners that slow down your development pipeline. Start your free continuous security scan with Penetrify today to see the difference. There's no credit card required to access our free tier, so you can begin hardening your applications immediately. You've got the roadmap to smarter security spending; now it's time to put it into action.
Frequently Asked Questions
How much does DAST software typically cost per year?
Annual costs for DAST software typically range from $2,500 to $20,000 per application. Enterprise-grade platforms like Burp Suite Enterprise start around $4,999 per year for basic scanning capabilities. If you need a fully managed service where experts handle the scanning, prices often exceed $50,000 annually. These figures depend on whether you choose a self-hosted scanner or a cloud-based SaaS model.
Is there a free DAST tool available for small businesses?
Yes, OWASP ZAP is the most widely used free DAST tool for small businesses. It's an open-source project maintained by a global community of developers. While it costs $0 in licensing fees, you'll need a security engineer to configure it. For 65 percent of small teams, the labor cost of managing a free tool outweighs the price of a commercial license.
What is the difference between DAST and SAST pricing?
DAST pricing usually focuses on the number of web applications or URLs scanned. In contrast, SAST tools often bill based on the number of contributing developers or total lines of code. A 2023 industry survey showed that SAST licenses average 15 percent more than DAST because they integrate earlier in the development lifecycle. This difference means dynamic application security testing pricing remains more predictable for teams with fixed application counts.
Do DAST tools charge per IP address or per application?
Most DAST vendors charge per application or Fully Qualified Domain Name rather than per IP address. Network vulnerability scanners use IP-based billing, but DAST focuses on the functional web layer. If your company runs 10 separate microservices on a single IP, you'll likely pay for 10 individual application licenses. About 80 percent of top-tier vendors follow this application-centric model.
Can I use DAST for PCI DSS compliance without a manual pen-test?
You can't replace a manual penetration test with DAST for PCI DSS Requirement 11.3. While DAST tools satisfy the quarterly scanning requirements in section 11.2, the PCI Security Standards Council explicitly requires a human-led test annually. Automated tools miss 30 percent of complex logic flaws that a human tester identifies during a 40-hour assessment. Use DAST as a continuous supplement, not a total replacement.
How does AI impact the price of dynamic application security testing?
AI integration typically increases the base cost of dynamic application security testing pricing by 20 to 30 percent. Vendors use AI to automate proof of exploit features, which reduces manual verification time by 4 hours per week. While the software is more expensive, you save money on labor. These intelligent scanners help teams find 12 percent more vulnerabilities compared to legacy rule-based engines.
What are the hidden costs of using open-source DAST scanners?
The biggest hidden cost is the engineering salary required to manage the tool. A security engineer earning $120,000 per year might spend 10 hours a week tuning an open-source scanner. This results in an indirect cost of $30,000 annually. You also lose money on false positives. Commercial tools have a 5 percent lower false-positive rate, saving developers 15 hours of wasted work every month.
Should I pay for a DAST tool or hire a penetration tester?
You should use both to ensure full security coverage. A DAST tool provides continuous scanning for $5,000 per year, while a manual penetration test costs between $10,000 and $25,000 per engagement. Use the automated tool for daily checks against common vulnerabilities. Hire a human tester once every 12 months to find high-level business logic errors that software simply can't detect.
