
What if the 4% global turnover fine isn't just a threat for tech giants but a direct consequence of your last missed software patch? You already know that securing personal data is non-negotiable; however, the line between a legal Data Protection Impact Assessment and a technical gdpr vulnerability assessment remains dangerously blurry for 70% of security teams. It's a common struggle because manual pentesting often takes 14 days to complete while your agile developers are pushing updates every few hours.
You don't have to choose between deployment speed and legal safety. This guide provides a clear roadmap to align your scanning tools with the strict technical mandates of Article 32 to ensure your infrastructure is fully compliant for 2026. We will examine the critical differences between Article 32 and Article 35 requirements while showing you how to automate your compliance to stop chasing vulnerabilities and start preventing them.
Key Takeaways
- Learn how to distinguish between Article 32 and Article 35 requirements to ensure your security measures meet specific GDPR legal standards.
- Understand how to implement Technical and Organisational Measures (TOMs) that guarantee the confidentiality and resilience of your data processing systems.
- Discover why moving beyond annual manual testing to a continuous gdpr vulnerability assessment is essential for meeting the mandate for regular security testing.
- Identify the specific DAST, SAST, and AI-driven tools needed to map and protect every endpoint that interacts with personal data.
- Explore how to transition from static, point-in-time audits to an "always-on" compliance posture using AI-powered automation.
What is a GDPR Vulnerability Assessment?
A gdpr vulnerability assessment is a systematic technical review designed to identify security gaps in systems that process personal data. It isn't just a best practice. It's a fundamental requirement for maintaining the integrity and confidentiality of European citizen data. Under the General Data Protection Regulation (GDPR), organizations must implement "state of the art" technical measures to protect sensitive information. This means that using outdated firewalls or unpatched software from 2021 is no longer legally defensible when modern exploits exist.
By 2026, the European Data Protection Board expects a definitive shift from annual point-in-time audits to continuous compliance monitoring. Static reports are becoming obsolete. Organizations now face an environment where over 30,000 websites are compromised daily. Real-time awareness of system weaknesses is vital for survival. A proactive gdpr vulnerability assessment ensures that you find the holes in your perimeter before a malicious actor does.
To better understand the core principles that drive these security requirements, watch this helpful video:
Article 32 vs. Article 35: Which one do you need?
Article 32 focuses on the security of processing. It mandates that controllers and processors implement technical measures like encryption and pseudonymization. This article specifically requires "regularly testing, assessing and evaluating" the effectiveness of these measures. In contrast, Article 35 deals with Data Protection Impact Assessments (DPIAs). A DPIA is necessary when a project involves high-risk processing, such as large-scale surveillance or processing biometric data. While they differ in scope, a technical assessment provides the empirical evidence needed to satisfy the legal requirements of a formal DPIA.
Key components of a GDPR-focused security audit
A robust audit begins with a comprehensive asset inventory. You can't protect data if you don't know where it resides. This includes identifying all servers, cloud buckets, and third-party APIs that touch EU personal data. Following discovery, technical scanning tools must probe for known exploits and configuration errors. Misconfigured cloud storage alone led to the exposure of over 100 million records in several high-profile 2023 breaches. Regular Testing is a mandatory GDPR requirement for all data controllers.
Adopting a "state of the art" posture requires moving beyond simple automated scans. True compliance involves manual verification of vulnerabilities to eliminate false positives. This process ensures that remediation efforts focus on the most critical risks first. When a regulator asks for proof of security, a documented history of these assessments serves as your primary defense. It demonstrates that your organization takes its duty of care seriously. Without this documentation, fines can reach 4% of global annual turnover or 20 million Euros. In 2023, the average cost of a data breach reached 4.45 million dollars, proving that the cost of prevention is far lower than the price of failure.
- Asset Identification: Cataloging every database and endpoint containing PII.
- Vulnerability Scanning: Using automated tools to find unpatched software.
- Risk Prioritization: Ranking flaws based on the sensitivity of the data they expose.
- Remediation Tracking: Proving that identified gaps were actually closed.
Compliance is a moving target. As new threats emerge, your assessment frequency must increase. The goal is to create a resilient infrastructure that protects user rights by default. By integrating these technical checks into your standard operations, you move from a reactive state to a position of strength.
The Technical Requirements of GDPR Article 32
Compliance begins with the legal framework established by GDPR Article 32, which mandates that organizations implement "appropriate technical and organisational measures" (TOMs) to ensure data security. For SaaS providers, this isn't a suggestion. It's a strict requirement to protect the confidentiality, integrity, availability, and resilience of processing systems. If your platform goes down due to a DDoS attack or a database is corrupted, you've failed the availability and integrity tests. These aren't just IT issues; they're direct violations of European law.
The stakes are high because data breaches remain the primary reason for regulatory action. Since May 2018, European authorities have issued over €4.5 billion in cumulative fines. A significant portion of these penalties stems from "insufficient technical and organizational measures to ensure information security." A proactive gdpr vulnerability assessment serves as your first line of defense. It identifies the gaps that hackers exploit before they turn into a headline-making breach. While Article 32 mentions encryption and pseudonymization, these are secondary safeguards. They protect data after a breach occurs, but they don't fulfill the obligation to prevent the breach in the first place.
- Confidentiality: Ensuring only authorized users access PII.
- Integrity: Protecting data from unauthorized alteration.
- Availability: Ensuring data is accessible when needed.
- Resilience: The ability of your infrastructure to withstand and recover from attacks.
Mapping OWASP Top 10 to GDPR Risks
Security flaws aren't just bugs; they're legal liabilities. An SQL Injection (SQLi) vulnerability is a direct path to a massive "unauthorized disclosure" fine. If an attacker can query your database through a web form, your confidentiality measures are non-existent. Broken Access Control is another frequent offender. It allows users to view data they shouldn't see, which violates the "data minimization" principle. Similarly, Cross-Site Scripting (XSS) allows attackers to inject malicious scripts into your site. This compromises the integrity of the user session and can lead to the theft of sensitive session tokens.
The 'State of the Art' Standard
Regulators in 2026 define "state of the art" by the current capabilities of the industry. Legacy manual testing performed once a year no longer satisfies the requirement for "regular testing, assessing and evaluating" security effectiveness. The 2023 Verizon Data Breach Investigations Report noted that 74% of breaches involve a human element or privilege misuse. This highlights why manual oversight alone fails. You must integrate a gdpr vulnerability assessment into your software development lifecycle (SDLC). By using tools to automate your security scanning, you ensure that every new code deployment meets the "state of the art" threshold without slowing down your release velocity. Continuous monitoring is now the expected baseline for any company handling European citizen data.
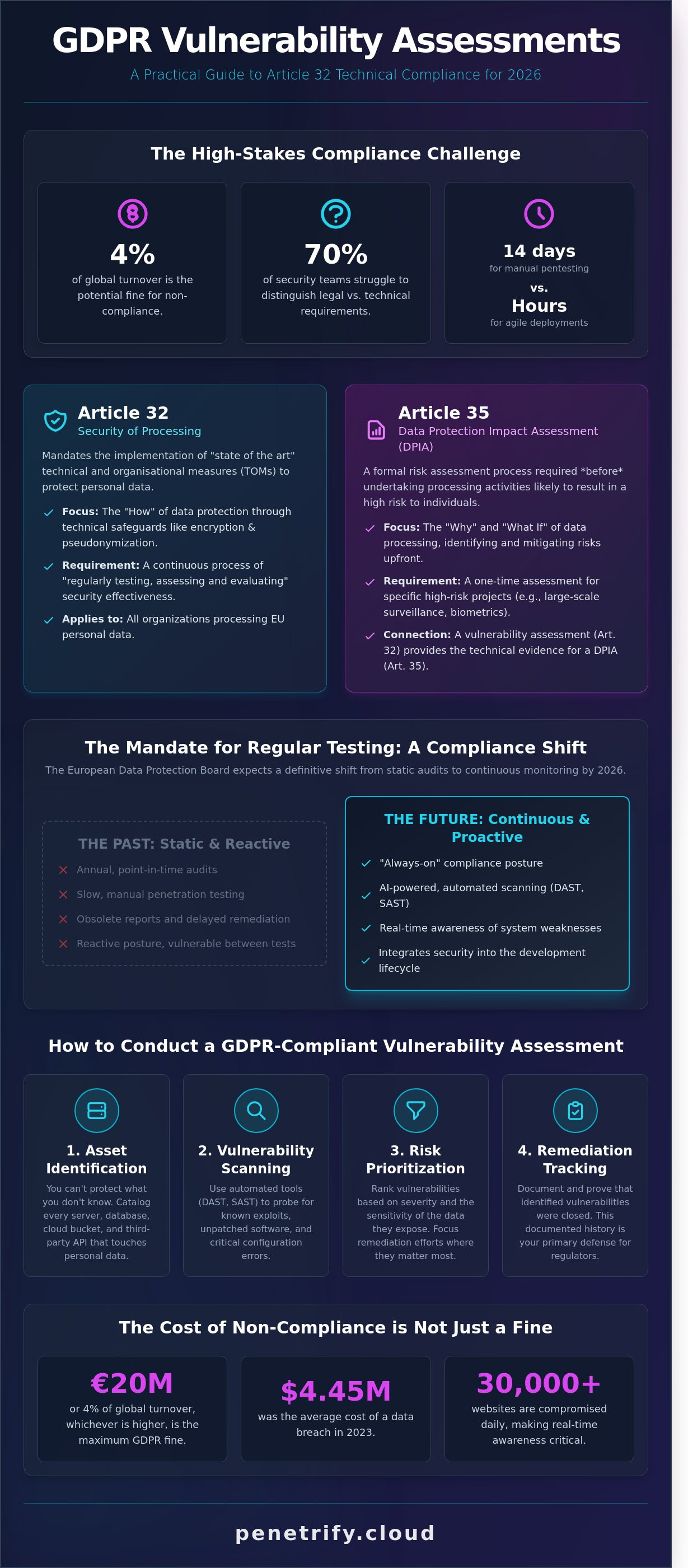
Manual vs. Automated Assessment: Meeting the 'Regular Testing' Mandate
GDPR Article 32 explicitly requires organizations to implement a process for regularly testing, assessing, and evaluating the effectiveness of technical and organizational measures for ensuring the security of processing. While many firms historically relied on an annual manual penetration test to check this box, that approach no longer satisfies the "regular" requirement in a fast-moving digital environment. A single point-in-time audit leaves a 364-day gap where new vulnerabilities can emerge and go undetected. Implementing a continuous gdpr vulnerability assessment strategy is the only way to maintain compliance between formal audits.
Traditional manual consulting remains valuable for its depth; a human expert can find complex logic flaws that software might miss. However, manual testing is expensive and slow. A standard manual engagement often costs between $15,000 and $30,000, making it impossible to perform weekly or even monthly. Automated scanning serves as the backbone of continuous data protection because it operates at a fraction of the cost and provides immediate feedback. By integrating Data Protection by Design, organizations ensure that security checks are built into the software lifecycle rather than added as an afterthought.
The most effective strategy is a hybrid approach. This balances the high-level frequency of automated scans with the surgical depth of manual testing. Automated gdpr vulnerability assessment tools can scan for thousands of known CVEs (Common Vulnerabilities and Exposures) every time code changes, while manual testers focus on high-stakes business logic once or twice a year. This dual-layered defense ensures that no obvious entry point remains open for long.
Why 'Once a Year' is no longer enough
Modern development relies on CI/CD pipelines where code is deployed dozens of times a day. A 2024 study showed that 74% of organizations push updates at least weekly. A static annual audit can't keep up with this pace. When a new Zero-Day vulnerability is discovered, it creates instant non-compliance. You can find a deeper methodology comparison in our guide on AI in Pentesting vs. Manual Pentesting to see how these speeds differ.
AI-Powered Agents: The 2026 Compliance Standard
By 2026, autonomous AI security agents will be the benchmark for GDPR compliance. These agents don't just scan; they simulate real-world attack paths to identify high-risk flaws that lead to data exfiltration. They reduce false positives by up to 70% compared to legacy scanners, which keeps compliance teams focused on legitimate threats. This technology allows a single platform to scale assessments across 100+ microservices simultaneously, something human teams can't match.
Transitioning to AI-powered agents also offers a significant cost-benefit advantage. While traditional consulting fees stay high regardless of results, AI agents provide 24/7 coverage for a predictable subscription fee. This shift reduces the total cost of ownership for security compliance by roughly 60% while increasing the frequency of testing from annually to daily. For any company handling sensitive European citizen data, this level of consistency isn't just a luxury; it's a core requirement for avoiding the heavy fines associated with data breaches.
- Manual Testing: Best for complex logic, high cost, low frequency.
- Automated Scanning: Best for known CVEs, low cost, high frequency.
- AI Agents: Best for attack simulation, moderate cost, continuous frequency.
How to Conduct a GDPR-Compliant Vulnerability Assessment
Executing a gdpr vulnerability assessment requires a shift from generic security scanning to data-centric testing. Article 32 of the GDPR mandates that organizations implement technical measures to ensure a level of security appropriate to the risk. This doesn't mean scanning your entire network with equal intensity. It means focusing your resources where personal data actually lives. You must demonstrate that you've tested the specific controls protecting EU residents' information to avoid the stiff penalties associated with non-compliance.
Step 1: Scoping for Data Privacy
Effective scoping begins by identifying your "Data Jewels." These are the databases, file shares, and applications containing PII like names, IP addresses, or biometric data. Your scope must include every endpoint that interacts with this data. Don't overlook third-party APIs or cloud storage buckets. According to the 2024 Verizon Data Breach Investigations Report, 68% of breaches involve a non-malicious human element or configuration error in these external connections. Documenting this scope is vital for proving due diligence during a regulatory audit. It shows you've mapped the data flow before starting the technical scan.
Once you've defined the scope, you need to select the right tools for the job. A comprehensive assessment uses a combination of three methodologies:
- SAST (Static Application Security Testing): This analyzes your source code for vulnerabilities before the application runs.
- DAST (Dynamic Application Security Testing): This tests the application from the outside in, mimicking how an attacker would interact with your web interfaces.
- AI-Driven Penetration Testing: This goes beyond automated scanning to find complex logic errors, such as Insecure Direct Object References (IDOR), which often lead to unauthorized data access.
During the execution phase, your team should test for common flaws identified in the OWASP Top 10. You aren't just looking for outdated software. You're searching for broken access controls that could allow one user to see another's personal profile. Testing logic errors is critical because automated scanners often miss the nuances of how data is processed between different microservices.
Step 4: Reporting for Auditors
Auditors don't want to see a 300-page PDF of raw scan data. They need a report that translates technical vulnerabilities into risk-based compliance language. You should categorize findings by their potential impact on data subjects. Use clear metrics like "Time-to-Remediate" (TTR) to show how quickly your team closes security gaps. Organizations that maintain a TTR of under 30 days for critical flaws demonstrate a proactive stance toward data protection. For more details on structuring these workflows, see our guide on The Complete Vulnerability Management Lifecycle.
The final stage is remediation and verification. After your team applies patches or configuration changes, you must re-scan the affected systems. Verification is a non-negotiable step in a gdpr vulnerability assessment. Industry data suggests that 25% of security patches are either applied incorrectly or fail to resolve the underlying issue on the first attempt. Re-scanning provides the evidence needed to close the loop in your audit trail. This documentation proves to supervisory authorities that your "state of the art" protections are functioning as intended.
Ready to secure your data and meet regulatory requirements with precision? Start your automated penetration test today to identify and fix vulnerabilities before they become compliance failures.
Continuous Compliance with Penetrify’s AI Platform
Achieving regulatory alignment isn't a one-off task that ends when a certificate is issued. Article 32 of the GDPR specifically demands that organizations implement a process for regularly testing, assessing, and evaluating the effectiveness of technical measures. Penetrify’s AI platform transforms this requirement from a manual burden into an automated standard. By conducting a continuous gdpr vulnerability assessment, the platform ensures that security gaps don't linger for months between annual audits. This shift is critical because 68% of data breaches involve a vulnerability that was known for weeks before the actual exploit occurred.
Moving from point-in-time audits to always-on protection is the only way to keep pace with modern software delivery. If your team deploys code 15 times a week, a quarterly scan leaves you exposed for 98% of the year. Penetrify closes this window by scanning every update in real-time. This provides the robust audit trail needed for GDPR inspections. When a Data Protection Authority (DPA) requests proof of your security posture, you can present a chronological log of every scan, identified risk, and successful remediation. This level of documentation demonstrates the "Accountability" principle required under Article 5(2) of the regulation.
For fast-growing development teams, scaling security often feels like a choice between speed and safety. Hiring manual penetration testers for every minor release is financially unsustainable, often costing upwards of $15,000 per engagement. Penetrify offers a cost-effective alternative by reducing the cost per assessment by approximately 85%. It allows teams to scale their infrastructure without a linear increase in security overhead. You get the depth of a manual expert with the speed of an automated script, ensuring that your compliance budget is spent on fixing problems rather than just finding them.
Real-time Visibility into Data Risks
Penetrify identifies OWASP Top 10 flaws, including broken access control and cryptographic failures, in less than 15 minutes. This speed allows CTOs to maintain development velocity while Compliance Officers receive the granular reporting they need to verify data protection standards. Penetrify's AI agents identify SQLi risks by autonomously probing database entry points to ensure no unauthorized queries can trigger a mandatory 72-hour breach notification to regulators. This proactive approach turns security into a measurable business asset rather than a vague insurance policy.
Future-Proofing Your Security Strategy
The regulatory landscape is shifting, and AI models within Penetrify update automatically to reflect the latest GDPR interpretations and emerging threat vectors. You don't need to manually reconfigure your settings when new vulnerabilities like Log4j emerge; the platform adapts its testing logic instantly. By integrating Penetrify directly into your existing CI/CD pipeline, you ensure that a gdpr vulnerability assessment happens every time code moves from a developer's laptop to the production environment. This integration prevents non-compliant code from ever reaching your customers, effectively baking security into the software development life cycle.
Don't wait for an audit to discover your security gaps. Start your first GDPR-focused vulnerability scan with Penetrify today and secure your path to continuous compliance.
Future-Proof Your Compliance Strategy
GDPR Article 32 explicitly requires a process for regularly testing and evaluating technical security measures. Waiting for an annual audit creates a 364-day gap where new exploits can compromise your sensitive data. Transitioning to a continuous gdpr vulnerability assessment model ensures you stay ahead of the 25,000 new security flaws identified by researchers each year. It's no longer enough to check a box once; you need real-time visibility into your risk profile to protect user privacy effectively.
Legacy testing cycles typically demand 4 to 6 weeks of coordination and manual reporting. Penetrify eliminates this bottleneck by delivering comprehensive OWASP Top 10 scanning results in less than 15 minutes. By integrating AI-driven automation, you satisfy the "Regular Testing" mandate while maintaining a 24/7 defense against evolving digital threats. Don't let outdated manual processes become your biggest compliance liability in 2026.
Automate your GDPR technical compliance with Penetrify's AI-powered platform.
Building a resilient security culture starts with the right tools. Take control of your technical requirements today and turn compliance into a competitive advantage for your business.
Frequently Asked Questions
Is a vulnerability assessment mandatory under GDPR?
GDPR Article 32 requires companies to implement a process for regularly testing, assessing, and evaluating the effectiveness of security measures. While the text doesn't explicitly use the phrase "vulnerability assessment," the European Data Protection Board Guidelines 01/2021 clarify that technical testing is essential for compliance. Organizations failing to perform these checks risk fines up to €20 million or 4% of global turnover. It's a non-negotiable part of data protection.
How often should I perform a GDPR vulnerability assessment?
You should conduct a gdpr vulnerability assessment at least once every 90 days to maintain a strong security posture. PCI DSS 4.0 standards recommend quarterly scans, and GDPR compliance follows similar rigorous cadences for high-risk data environments. If you deploy new code or change your network architecture, you must run a fresh assessment within 24 hours to ensure no new security gaps exist. Regularity proves your commitment to security.
What is the difference between a vulnerability scan and a DPIA?
A vulnerability scan is a technical automated process that identifies software weaknesses like SQL injection or outdated SSL certificates. In contrast, a Data Protection Impact Assessment (DPIA) is a legal requirement under Article 35 for high-risk processing. While a scan takes minutes to complete, a DPIA involves a multi-step risk analysis of the entire data lifecycle. Both are necessary to satisfy 100% of GDPR accountability requirements and protect user privacy.
Can automated tools replace manual penetration testing for GDPR?
Automated tools can't replace manual penetration testing because they miss complex logic flaws that 80% of human testers identify. Automation handles the 1,000+ known CVEs efficiently, but manual testing uncovers zero-day exploits and business logic errors. For robust GDPR compliance, use automated scans weekly and schedule manual penetration tests at least once per year. This dual approach ensures you validate your technical defenses against sophisticated cyberattacks that bots often miss.
What happens if a vulnerability assessment finds a critical flaw?
You must document the finding in your risk register and initiate a remediation plan within 24 to 72 hours for critical vulnerabilities. GDPR's principle of integrity and confidentiality means leaving a known flaw unpatched is a direct compliance violation. If the flaw led to data exposure, you have exactly 72 hours to notify the relevant supervisory authority according to Article 33 guidelines. Immediate action prevents minor bugs from becoming massive legal liabilities.
Does GDPR require external third-party assessments?
GDPR doesn't explicitly mandate third-party auditors, but using external experts provides the objective evidence required by Article 32. Internal teams often overlook 15% to 20% of vulnerabilities due to familiarity bias or limited internal tools. Relying on an external provider helps demonstrate state of the art security to regulators. This external validation is vital if you face an audit following a reported security incident or a significant data breach.
How do I document a vulnerability assessment for a GDPR audit?
Create a comprehensive report that includes the scan date, the specific assets tested, and a list of identified risks categorized by CVSS scores. You must also include a remediation log showing that you fixed 100% of critical issues. Save these records for 5 years to prove a history of continuous monitoring. This documentation serves as primary evidence that your gdpr vulnerability assessment process meets the accountability standards set by EU regulators.