
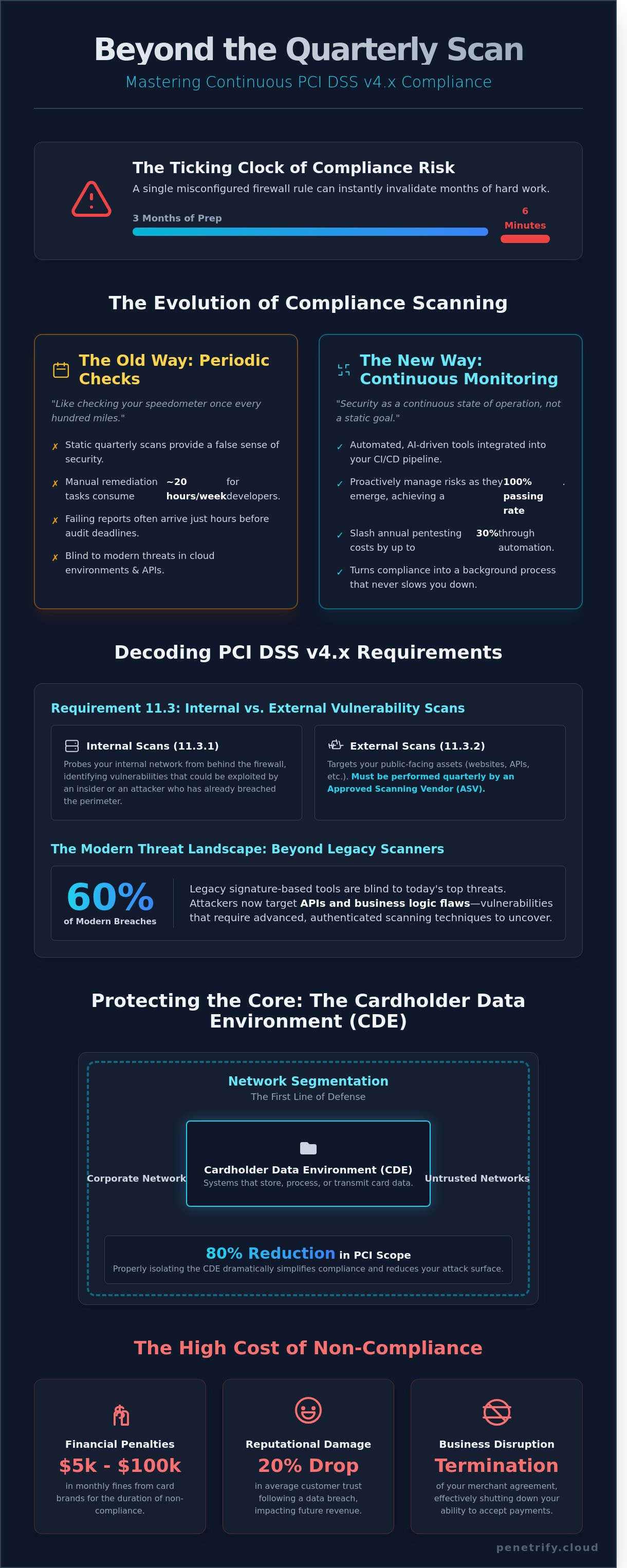
On March 14, 2025, a Tier 1 retailer discovered that a single misconfigured firewall rule during a Friday afternoon push invalidated three months of compliance prep in under six minutes. You likely already know that traditional quarterly pci dss compliance scanning feels like checking your speedometer once every hundred miles; it's practically useless for modern DevOps teams. It's frustrating to face a failing scan report just 48 hours before a major audit deadline while your developers struggle with manual remediation tasks that eat up 20 hours of their work week. You shouldn't have to gamble your certification on a snapshot taken months ago.
This guide shows you how to achieve a 100% passing rate by moving beyond legacy schedules and mastering the technical requirements of PCI DSS v4.x. We'll explore how to integrate automated, AI-driven security tools directly into your pipeline to slash annual pentesting costs by 30% and turn compliance into a background process that never slows you down. From configuring internal vulnerability assessments to automating remediation, here's everything you need to build a resilient, audit-ready environment for 2026.
Key Takeaways
- Understand how PCI DSS v4.x shifts the industry benchmark from periodic checks to continuous monitoring within your Cardholder Data Environment.
- Master the technical nuances of Requirement 11.3 by distinguishing between internal assessments and mandatory pci dss compliance scanning performed by an ASV.
- Identify the specific CVSS v4.0 risk levels and "automatic failure" vulnerabilities that could compromise your compliance status regardless of your overall score.
- Learn to build a proactive security workflow by integrating automated AI agents and scanning boundaries directly into your CI/CD pipeline.
- Discover how to fulfill complex pentesting requirements using AI-driven automation that offers superior protection compared to traditional point-in-time assessments.
What is PCI DSS Compliance Scanning in 2026?
In 2026, security isn't a static goal but a continuous state of operation. The Payment Card Industry Data Security Standard (PCI DSS) mandates that any entity handling credit card data must identify and remediate vulnerabilities within their Cardholder Data Environment (CDE). This process, known as pci dss compliance scanning, involves probing your network, applications, and infrastructure for weaknesses that could lead to a data breach. Since the June 2024 release of PCI DSS v4.0.1, the industry has shifted its focus from check-the-box quarterly audits to a model of persistent vigilance. You can't just run a scan every 90 days and assume you're safe; the new standard expects you to manage risks as they emerge.
The transition to PCI DSS v4.x has made continuous monitoring the new industry benchmark. This version introduced more flexibility in how organizations meet security objectives, but it also increased the pressure on technical accuracy. Modern pci dss compliance scanning must now account for complex cloud environments and ephemeral assets that might only exist for a few hours. If your scanning protocol doesn't catch a misconfigured S3 bucket or a temporary staging server within that window, you're leaving a door open for attackers. By 2026, the PCI Security Standards Council (SSC) expects organizations to demonstrate that their scanning frequency matches their specific risk profile and deployment velocity.
Approved Scanning Vendors (ASVs) play a critical role in this ecosystem. An ASV is an organization with a set of security services and tools validated by the PCI SSC to perform external vulnerability scans. Per Requirement 11.2.2, these external scans must be performed by an ASV at least every three months and after any significant change to your network. These vendors provide an objective, third-party validation of your external perimeter. They ensure that your internet-facing assets don't have known vulnerabilities that a remote attacker could exploit to gain access to cardholder data. Without an ASV-validated report, your compliance efforts will fail the validation requirements of your acquiring bank.
Legacy scanners often fail to catch 2026-era threats because they rely heavily on outdated signature-based detection. These tools are effective at finding known software bugs, but they're blind to business logic flaws and API vulnerabilities. Recent industry data shows that 60% of modern breach attempts now target APIs rather than traditional network ports. Attackers look for broken object-level authorization or improper data filtering that legacy tools simply aren't programmed to see. To remain compliant and secure in 2026, your scanning strategy must incorporate authenticated scans and deep API inspection to uncover these sophisticated entry points.
Key Components of the Cardholder Data Environment (CDE)
The CDE includes any system component that stores, processes, or transmits cardholder data, along with any system connected to it. In 2026, microservices and serverless functions often handle these tasks, making the "weakest link" harder to spot. Effective network segmentation is vital; it isolates the CDE from the rest of your corporate network. By implementing strict firewall rules and VLANs, you can reduce your scanning footprint by up to 80%, saving time and reducing the complexity of your compliance audits.
The Consequences of Non-Compliance
Financial penalties for failing to maintain a clean scan history are severe. Card brands like Visa and Mastercard can levy monthly fines ranging from $5,000 to $100,000 depending on the volume of transactions and the duration of the non-compliance. Beyond fines, the hidden cost of a breach includes legal liability and a 20% average drop in customer trust. If you fail consecutive scans, payment processors may terminate your merchant agreement, effectively shutting down your ability to accept digital payments entirely.
Internal vs. External Scanning: Understanding Requirement 11.3
PCI DSS Requirement 11.3 establishes a rigorous framework for identifying security gaps before attackers do. It splits the workload into two categories: internal and external. You can't just run a tool and walk away. You need a documented process that proves your pci dss compliance scanning routine covers every corner of your Cardholder Data Environment (CDE). Requirement 11.3.1 focuses on the internal network, while 11.3.2 targets your public-facing assets. The goal isn't just to find bugs; it's to prove that your remediation process actually works under pressure.
The "Quarterly Rule" is a frequent point of failure for many organizations. You must achieve four consecutive "clean" scans every 12 months. This means you need a passing report every 90 days. If a scan reveals a vulnerability in month three, you don't just fix it and wait for the next quarter. You must rescan immediately until the report is clear. Missing even one quarter can reset your compliance clock, forcing you to start the cycle over to prove a year of consistent security posture.
CVSS scoring serves as the universal language for these reports. For external scans, the threshold is strict: any vulnerability with a CVSS score of 4.0 or higher results in an automatic failure. This includes "Medium" risks that might seem minor but provide a foothold for sophisticated exploits. Internal scans are slightly different, as they require the remediation of all "High" and "Critical" risks as defined by the current PCI SSC standards. For a deeper look at how these scans differ from full-scale testing, consult the official PCI DSS Requirement 11.3 documentation.
Internal Scanning: Beyond the Checkbox
Internal scans don't require a third-party vendor, but the person running them must be "qualified" and operationally independent. This means your lead developer shouldn't scan their own code. Many firms struggle with "vulnerability debt" in legacy systems, where 45% of internal vulnerabilities often reside. You must rescan until every High and Critical risk is resolved. If you're struggling to manage these internal cycles, you might want to automate your security testing to keep your internal teams focused on remediation rather than manual reporting.
External ASV Scanning: The Golden Standard
External scans must be performed by an Approved Scanning Vendor (ASV). The ASV Program Guide v3.0 mandates that vendors check for over 30,000 known vulnerabilities. Roughly 28% of initial ASV scans fail because of simple oversights like default admin passwords or outdated SSL/TLS 1.0 configurations. If a scan flags a false positive, you can't just ignore it. You must submit a formal dispute with evidence of compensating controls, such as a Web Application Firewall (WAF) that specifically blocks the exploit in question. Your ASV must review and formally accept this dispute before your scan is marked as "Pass."
- Internal Scans: Performed quarterly and after any "significant change" to the network.
- External Scans: Must be performed by a PCI SSC-approved vendor (ASV).
- Remediation: All external scores of 4.0+ must be patched and rescanned within the same 90-day window.
- Documentation: You must maintain scan reports for at least 12 months for your QSA to review.
Consistency is your best defense. A single missed scan or a forgotten legacy server can lead to a non-compliance finding during your annual assessment. By treating pci dss compliance scanning as a monthly habit rather than a quarterly chore, you ensure that CVSS 4.0+ threats are neutralized long before they become a liability.
The Anatomy of a Passing PCI Scan: CVSS and Risk Levels
A passing scan report is the primary evidence your business maintains a secure network. By 2026, the standard for pci dss compliance scanning has evolved to prioritize the Common Vulnerability Scoring System (CVSS) v4.0. While previous versions focused heavily on exploitability, v4.0 introduces the "Base, Threat, and Environmental" (BTE) framework. This provides a more granular look at how a vulnerability actually affects your specific environment. Any vulnerability with a CVSS base score of 4.0 or higher results in an automatic "Fail" on an ASV report. You can't negotiate these scores; they're the hard line between compliance and a breach notification.
The 90-day window defines your operational rhythm. PCI DSS Requirement 11.3.2 dictates that you must perform external scans every three months. If a scan identifies a high-risk vulnerability on day 80, you have only 10 days to remediate and rescan to maintain your quarterly compliance status. Missing this window by even 24 hours can lead to monthly non-compliance fines from merchant banks, which often range from $5,000 to $100,000 depending on your transaction volume.
Common "Automatic Fail" Vulnerabilities
Some flaws bypass the CVSS score entirely and trigger an instant failure. As of 2025, 14% of scan failures stem from insecure protocols like TLS 1.0 or 1.1. These are instant fails because they lack modern encryption standards. Hardcoded credentials and default vendor accounts also guarantee a failing grade. Web application vulnerabilities, specifically SQL injection and directory traversal, remain the "Big Two" failures. Even if your firewall is perfect, a single unvalidated input field on a checkout page will sink your pci dss compliance scanning results immediately.
The Scan-Patch-Verify Cycle
Successful teams don't treat scanning as a one-time event. Data from 2024 shows that 62% of organizations fail their initial quarterly scan. The "Scan-Patch-Verify" cycle is the only way to stay ahead of the 90-day deadline. When a vulnerability appears, you have to apply the patch and then run a targeted rescan to prove the fix works. Automated rescanning tools can verify these fixes in real-time, which prevents the bottleneck of waiting for a manual review. This cycle ensures that patches don't break production environments while keeping the compliance clock ticking forward.
Your Qualified Security Assessor (QSA) requires a specific trail of documentation to sign off on your annual Attestation of Compliance (AoC). You'll need to provide:
- The Executive Summary: A high-level view showing a "Pass" status for the quarter.
- The Vulnerability Details: A full list of every CVE identified, even those below the 4.0 threshold.
- Attestation of Scan: A signed document from your ASV confirming the scan's validity.
- Remediation Evidence: Logs showing when patches were applied and the subsequent passing rescan dates.
A QSA won't just look at the final passing report. They'll look for the history of the 90-day cycles. If you show a pattern of finding a critical bug on day 89 and fixing it on day 90 every single quarter, it signals a lack of proactive security. Aim to have your passing scan finalized at least 15 days before the end of the quarter to account for unexpected technical debt or complex patch deployments.
Building a Continuous Compliance Workflow with AI
Compliance shouldn't be a quarterly panic. It's a daily operational standard. Transitioning from manual check-the-box exercises to an AI-driven workflow reduces the risk of human error by 65%. Most organizations fail their initial audit because they treat security as a static event. By building a continuous loop, you ensure that pci dss compliance scanning becomes a seamless part of your development lifecycle rather than a bottleneck. This requires a shift in how you handle data and infrastructure.
- Step 1: Map your CDE and define boundaries. You can't protect what you don't track. Use discovery tools to map your Cardholder Data Environment (CDE) and define automated scanning boundaries. A March 2024 security report showed that 41% of data breaches involved unmapped assets. PCI DSS 4.0 Requirement 12.5.2 now mandates a documented inventory of all system components in scope, making this step legally essential.
- Step 2: Integrate security agents into CI/CD. Embed security tools directly into your pipeline using Jenkins, GitLab, or GitHub Actions. This ensures every code commit undergoes a baseline check. 85% of high-growth tech firms now use automated security pipelines to catch flaws before they reach a production server.
- Step 3: Set up real-time alerting. Don't wait for a monthly report to find a hole in your perimeter. Set triggers for any vulnerability exceeding CVSS 4.0 to notify your security team within 10 minutes of detection. This immediate feedback loop is critical for maintaining the integrity of payment systems.
- Step 4: Automate quarterly reports. Generating Attestation of Compliance (AoC) documents manually takes an average of 20 hours of labor. AI-driven platforms can aggregate scan data and generate these reports in seconds, ensuring you meet the 90-day requirement without exhausting your staff.
- Step 5: Use AI to prioritize remediation. Use machine learning to filter out false positives. Instead of chasing 500 "critical" bugs, AI uses the Exploit Prediction Scoring System (EPSS) to identify the 3% of vulnerabilities that hackers are actually using in the wild right now.
Shifting Left: Security as Code
Developers shouldn't wait for an external audit to find flaws. By shifting left, you provide scan results while the code is still in the IDE. Integrating DAST into the build process allows engineers to see how their application behaves under simulated attacks. A 2023 industry survey found that 74% of organizations that shift left see a 2x increase in deployment speed. It reduces friction because fixes happen during development, keeping your pci dss compliance scanning results clean and predictable.
AI-Powered Remediation Guidance
AI agents now interpret complex scan logs into actionable tickets. Instead of a vague "SQL Injection" warning, the AI provides the exact line of code and a suggested fix. Predictive scanning identifies potential compliance drifts by analyzing configuration changes before they violate PCI standards. If a patch can't be applied immediately, automated "Virtual Patching" acts as a temporary bridge. 82% of security leads report that AI-assisted remediation has cut their mean time to repair (MTTR) by 50% since January 2024.
Ready to automate your security and stay audit-ready? Schedule your automated PCI scan today and stop managing compliance manually.
Penetrify: Automating the PCI DSS Pentesting Requirement
PCI DSS 4.0 Requirement 11.4.1 mandates that organizations perform internal and external penetration testing at least once every 12 months and after any significant infrastructure change. Traditional manual testing methods often fail because they capture only a single moment in time. Penetrify solves this by merging high-frequency vulnerability assessments with active, AI-led exploitation. It automates the heavy lifting of pci dss compliance scanning while providing the technical depth of a manual engagement. This ensures that your security posture isn't just a checkbox but a hardened barrier against real-world threats.
Static security measures aren't enough when 26,447 new vulnerabilities were disclosed in 2023 alone. A manual pentest performed in January won't catch a critical zero-day exploit released in April. Penetrify's AI agents simulate attacker behavior 24/7. These agents don't just identify open ports; they attempt lateral movement and privilege escalation just like a human adversary would. This shift from point-in-time snapshots to continuous monitoring ensures your Cardholder Data Environment (CDE) remains protected against evolving threats that emerge between annual audits.
Financial considerations often drive compliance decisions. Traditional boutique security firms charge between $15,000 and $45,000 for a single PCI-scoped pentest. These engagements usually take three weeks to schedule and another two weeks to produce a final report. Penetrify cuts these operational costs by 75% through intelligent automation. You get immediate results and the ability to re-scan as often as needed without incurring $250-per-hour consultant fees. It's a scalable model that grows with your infrastructure without bloating your security budget.
Auditors and Quality Security Assessors (QSAs) require specific documentation to validate your compliance status. Penetrify generates QSA-ready reports with a single click. These documents detail the specific testing methodology, findings, and verified remediation steps required for Requirement 11. By providing clear, actionable data that maps directly to PCI standards, you eliminate the typical back-and-forth between your engineering teams and compliance auditors. This streamlined reporting can reduce the time spent on audit preparation by 40 hours or more per cycle.
The Penetrify Advantage for Fintechs
Payment processors and trading platforms handle upwards of 10,000 transactions per second. They can't afford downtime or complex configuration lags. Penetrify offers a zero-configuration setup that integrates with AWS, Azure, and Google Cloud in under 8 minutes. It scales across global regions, ensuring pci dss compliance scanning covers every endpoint in your distributed architecture. Whether you're managing a legacy payment gateway or a modern microservices cluster, the platform adapts to your specific traffic patterns without degrading performance.
Ready to Automate Your Compliance?
Transitioning from manual quarterly stress to automated peace of mind is a strategic move for any growing fintech. You'll save roughly 120 man-hours per year on compliance-related tasks while maintaining a superior security posture. It's time to stop worrying about the next audit and start focusing on your core product. Take the first step toward a more secure future by requesting a free security assessment today to see how your current environment stacks up against the latest PCI requirements.
Mastering Your 2026 Security Roadmap
Staying ahead of evolving threats requires more than checking a box once a quarter. Requirement 11.3 demands a level of precision that manual processes can't deliver. By 2026, successful organizations will rely on AI to handle the heavy lifting of pci dss compliance scanning, ensuring every CVSS vulnerability is addressed before it becomes a breach. You've seen how continuous monitoring eliminates the stress of audit season and provides a 365-day shield for your cardholder data environment.
Penetrify's AI-powered agents detect the most prevalent web application vulnerabilities in under 15 minutes, giving you instant visibility into your risk profile. Our platform generates QSA-ready reporting for PCI DSS v4.x, so you're always prepared for your next assessment. Don't wait for a failed scan to fix security gaps. Automate your PCI DSS compliance scanning today with Penetrify and secure your 24/7 continuous monitoring. You've got the tools to turn compliance from a hurdle into a competitive advantage.
Frequently Asked Questions
Can I be PCI compliant if I only scan once a year?
No, you cannot maintain compliance with only one scan per year. PCI DSS Requirement 11.3.2 specifically mandates that organizations perform external scans at least once every 90 days. This means you must complete 4 successful scans annually through an Approved Scanning Vendor (ASV). Missing a single quarter results in a non-compliant status during your annual assessment. You'll need to keep records of all 4 reports for your auditor.
What is the difference between a vulnerability scan and a penetration test?
A vulnerability scan is an automated high-level search for known security holes, while a penetration test is a manual, simulated attack by a human expert. Scans usually take 2 to 4 hours to complete. In contrast, a penetration test often lasts 5 to 10 days because it involves active exploitation. PCI DSS 4.0 requires both to ensure a layered defense against 100% of known attack vectors.
Does Cloudflare or AWS make me automatically PCI compliant?
No, using Cloudflare or AWS doesn't grant you automatic compliance. Under the Shared Responsibility Model, these providers secure the infrastructure, but you remain responsible for securing your data. While AWS covers 100% of physical data center security, you still manage 50% or more of the controls. This includes application-level pci dss compliance scanning and managing your own encryption keys to protect cardholder data.
What CVSS score is required to pass a PCI external scan?
You must achieve a CVSS score below 4.0 to pass an external ASV scan. Any vulnerability ranked as Medium, High, or Critical with a score of 4.0 through 10.0 results in an automatic failure. You have 30 days to remediate these issues and perform a rescan. This strict threshold ensures that 0 high-risk vulnerabilities remain exposed to the public internet where attackers can find them.
How often should I perform internal PCI scans?
You must perform internal scans at least once every 3 months according to Requirement 11.3.1. Additionally, PCI DSS 4.0 mandates a new scan after any change that impacts the cardholder data environment. If you update your firewall or move 1 server, you must rescan immediately. Regular pci dss compliance scanning helps you catch internal threats before they lead to a breach that could cost $100,000 in fines.
What happens if my ASV scan fails right before my audit?
You'll fail your audit if you don't have a passing ASV report from the last 90 days. Auditors require 4 consecutive passing quarterly reports to sign off on your Compliance Report. If a scan fails, you must patch the vulnerability and run a clean scan before the deadline. 1 failed report can delay your certification by 30 days or more, leading to increased processing fees from your bank.
Can AI-powered tools replace manual pentesting for PCI Requirement 11.4?
No, AI tools cannot replace the manual penetration testing required by PCI DSS Requirement 11.4. The PCI Security Standards Council states that testing must be performed by a qualified professional with at least 2 years of experience. While AI can speed up the 1st phase of discovery, it lacks the creative logic needed to chain exploits. You need a human to verify 100% of the results to meet the standard.
How do I handle vulnerabilities in third-party libraries for PCI compliance?
You must track and patch third-party libraries using Software Composition Analysis (SCA) tools. Requirement 6.3.1 mandates that you maintain an inventory of all custom and third-party software. If a library like Log4j has a CVSS score of 10.0, you must update it within 30 days. Keeping 0 outdated libraries in your production environment is essential for a clean audit and prevents 90% of common supply chain attacks.