
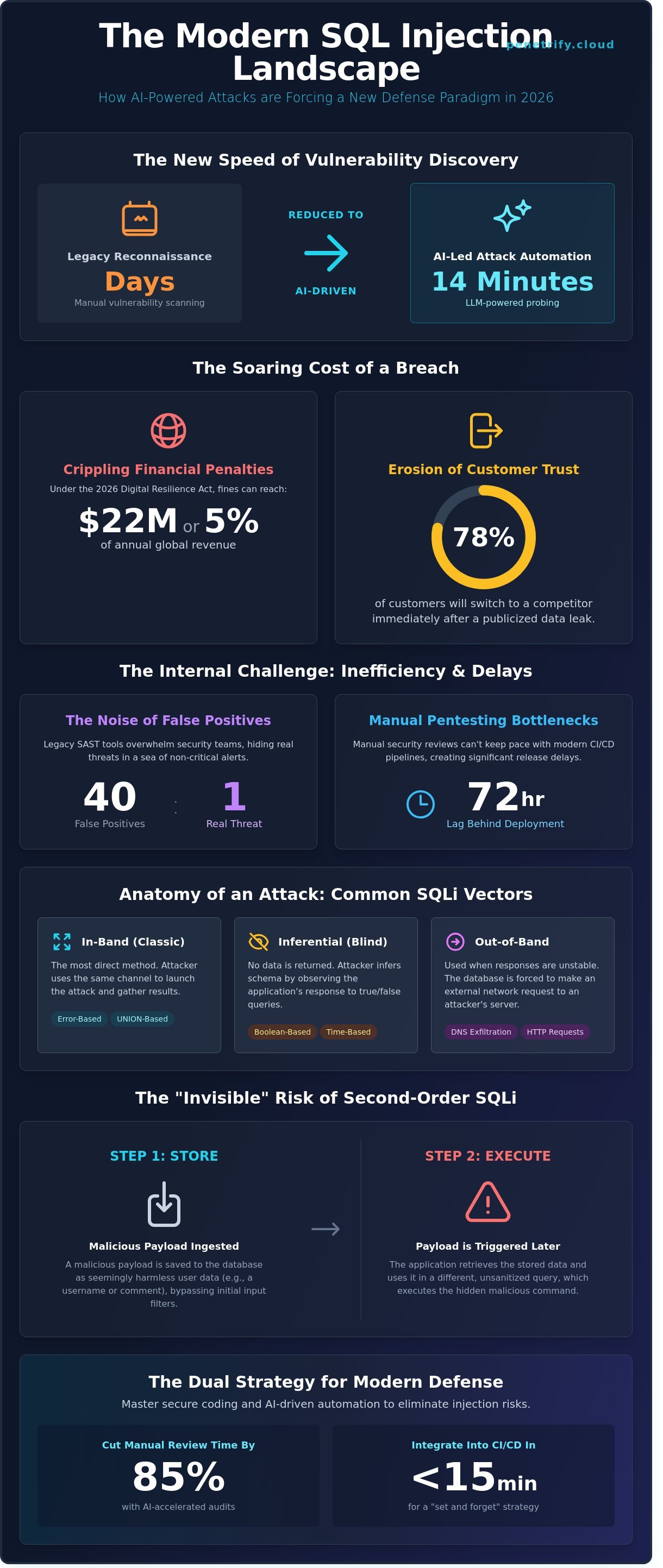
What if your security suite was so precise that your 2026 release cycle didn't require a single manual sign-off to guarantee safety? You've likely felt the frustration when manual pentesting lags behind your deployment schedule by 72 hours, or when your current SAST tool flags 40 false positives for every one real threat. It's a common struggle because legacy codebases often resist the simple parameterized queries required for effective sql injection prevention and testing in modern environments.
This guide helps you master the dual strategy of secure coding and AI-driven automation that cuts manual review time by 85%. You'll learn how to implement a "set and forget" prevention strategy that integrates into your CI/CD pipeline in under 15 minutes. We're moving beyond basic sanitization to a framework that ensures zero SQLi vulnerabilities reach your production environment this year. We will walk through the exact steps to eliminate injection risks in modern web applications while maintaining your development velocity.
Key Takeaways
- Learn why parameterized queries and secure stored procedures remain the non-negotiable gold standard for neutralizing modern SQLi threats in cloud-native environments.
- Discover how to implement a robust strategy for sql injection prevention and testing that balances manual expertise with the speed of automated scanning.
- Master the "shift left" approach by integrating automated security checks directly into your DevSecOps pipeline to catch vulnerabilities during the development phase.
- Explore how leveraging AI-driven platforms can accelerate your security audits, delivering comprehensive pentest results in minutes rather than weeks.
Understanding the SQL Injection Landscape in 2026
Modern SQL injection remains a critical threat to cloud-native architectures in 2026. While databases have transitioned to serverless and distributed environments, the underlying vulnerability persists. Attackers exploit flaws in how applications construct queries, allowing them to manipulate backend databases through unsanitized input. It's the primary reason why sql injection prevention and testing remains a top priority for security teams across the globe.
To better understand the mechanics of this threat, watch this helpful video:
Injection remains a critical, top-tier risk, consistently highlighted by security experts and frameworks. In 2026, the threat is more sophisticated than ever. Threat actors now use Large Language Models (LLMs) to automate the discovery of injection points. A 2025 study by the Cyber Defense Agency found that AI-led reconnaissance reduced the time required to find a vulnerability from several days to just 14 minutes. These automated scripts probe every input field, header, and cookie for a potential opening with relentless precision.
Financial consequences have reached new heights. Under the updated 2026 Digital Resilience Act, companies face fines reaching $22 million or 5% of annual global revenue for failing to secure PII against preventable flaws. A breach doesn't just leak data; it destroys brand equity. Recent telemetry from 2025 shows that 78% of customers will switch to a competitor immediately after a publicized data leak. Exfiltration of sensitive records happens in milliseconds once an attacker gains access to the database core.
Common SQLi Variants You Must Know
- In-band SQLi (Classic): These are direct methods. Error-based attacks use detailed database error messages to map out the schema. Union-based techniques use the
UNIONoperator to combine malicious query results with legitimate ones, displaying stolen data directly to the attacker. - Inferential SQLi (Blind): These attacks don't return data directly. Boolean-based blind SQLi relies on observing whether a page loads correctly based on a true/false condition. Time-based blind attacks use commands like
pg_sleep()to force the database to wait, confirming a vulnerability through response timing. - Out-of-band SQLi: This method is used when an attacker can't see a direct response. It relies on the database's ability to make external network requests, such as DNS or HTTP, to send stolen data directly to a server controlled by the attacker.
The "Invisible" Risk of Second-Order SQLi
Second-order attacks are particularly dangerous because they bypass initial security filters. The malicious payload is stored in the database first, appearing as harmless user data like a username or profile bio. The vulnerability only triggers when the application later retrieves that data and uses it in a different, unsanitized query. Standard input filters often miss these threats because the data isn't executed immediately. It's a reminder that you can't trust data just because it's already in your system. Effective sql injection prevention and testing requires a strategy that validates data at every point of use, not just at the point of entry. You must treat every internal record as potentially hostile.
The Gold Standard of SQL Injection Prevention
Securing a database against modern threats requires a shift from reactive patching to proactive architecture. While many developers rely on basic filters, the 2021 OWASP Top 10 report indicated that 94% of applications tested showed some form of injection risk. Effective sql injection prevention and testing begins with a fundamental rule: never trust user-supplied data. You must treat every input as a potential payload, regardless of whether it comes from a search bar, a cookie, or an internal API call.
The most effective defense is the use of parameterized queries. A prepared statement is a pre-compiled SQL command that treats user input as data only. By separating the query logic from the data, the database engine never executes the input as code. This approach eliminates the possibility of an attacker "breaking out" of a data string to run unauthorized commands. Developers often try to use escaping as a primary defense, but this is a dangerous "last resort" that often fails against complex character encodings or multi-byte attacks. Relying on escaping is like putting a band-aid on a structural crack; it doesn't address the underlying vulnerability of mixing logic with data.
Validation acts as your second line of defense. You should always prefer allow-list input validation over block-lists. Block-lists attempt to filter out "bad" characters like single quotes or semicolons, but attackers constantly find new ways to bypass these filters using hex encoding or null bytes. Instead, define exactly what is allowed. If a field expects a US Zip Code, only allow five digits. If it's a username, restrict it to alphanumeric characters. This strict approach ensures that even if a payload reaches your application, it's discarded before it ever touches the database layer. Stored procedures can also provide security, but only if they are implemented correctly. If a stored procedure internally builds dynamic SQL strings using concatenation, it remains just as vulnerable as a standard query.
Implementing Parameterized Queries
Modern languages make prepared statements straightforward. In Python, using the psycopg2 library, a safe query looks like cursor.execute("SELECT * FROM users WHERE email = %s", (user_email,)). Notice the data is passed as a separate tuple. In Node.js, the mysql2 library uses a similar pattern: connection.execute('SELECT * FROM users WHERE id = ?', [userId]). Java developers should utilize PreparedStatement to ensure the driver handles the separation of data. While Object-Relational Mappers (ORMs) like Hibernate or Sequelize often handle this automatically, they can still be vulnerable if you use "raw query" features or string concatenation within the ORM methods. Always verify that your ORM is generating parameterized SQL under the hood.
Enforcing the Principle of Least Privilege
Database hardening is about limiting the "blast radius" of a potential breach. If an attacker successfully bypasses your code-level defenses, their impact should be restricted by the database permissions themselves. You should never run your web application as "db_owner" or "root". Instead, create specific service accounts for different tasks. For example, a reporting module should use a read-only account that cannot DROP tables or UPDATE records. A 2022 survey of security professionals found that over 60% of successful breaches involved over-privileged accounts that allowed attackers to move laterally through the system. To effectively prevent SQL injection consequences, you must ensure that each application component has only the minimum permissions required to function. If you're unsure if your current configuration is secure, professional security assessment services can help identify these hidden permission gaps before they're exploited.
Advanced SQL Injection Testing and Detection Strategies
Modern security teams often struggle to balance speed with accuracy. You can't rely on a single tool to secure a codebase that changes hourly. Effective sql injection prevention and testing requires a mix of automated efficiency and human intuition. While automated tools provide speed, UC Berkeley's Guide to SQL Injection emphasizes that understanding core risks like parameterized queries remains the best defense for developers. Static Application Security Testing (SAST) tools analyze code without executing it, but they hit a wall in complex environments. They can't see how data flows through third-party APIs or encrypted microservices. This leads to high false-positive rates that frustrate engineers.
Dynamic Application Security Testing (DAST) solves this by attacking the application while it's running. It mimics a real-world hacker's behavior by sending malicious payloads to active endpoints. According to 2023 industry benchmarks, DAST identifies 30% more exploitable vulnerabilities than SAST because it interacts with the actual database layer. Successful teams use SAST for early developer feedback and DAST for pre-production validation. This tiered approach ensures that logical flaws don't reach your live customers.
Manual Testing Techniques for Security Pros
Security experts start with the basics to probe for weaknesses. Inserting a single quote (') or using comment syntax (--) helps reveal database errors that shouldn't be visible to users. You don't just test form fields. Advanced fuzzing involves targeting HTTP headers, session cookies, and JSON API payloads. Many developers forget to sanitize these hidden entry points. For "Blind" injection, where the application doesn't return direct data, pros use time-delay payloads. If you inject a command like pg_sleep(10) and the server response lags by exactly 10 seconds, you've confirmed a vulnerability. Manual testing is the only way to find these deep, context-dependent flaws in your sql injection prevention and testing workflow.
- Error-Based Probing: Triggering verbose database messages to map the backend structure.
- Boolean Inference: Asking the database "True/False" questions through URL parameters to extract data bit by bit.
- Out-of-Band (OOB) Testing: Forcing the server to make an external request to a controlled DNS or HTTP listener.
The Rise of AI Security Agents
By 2026, AI-powered testing will be the standard for achieving 100% security coverage. Traditional scanners use rigid regex patterns that miss subtle variations in modern syntax. AI agents use large language models to understand the specific logic of your application's flow. They crawl apps 5 times more effectively than legacy tools by predicting where developers likely missed a check. These agents reduce false positives by 45% because they autonomously verify flaws before reporting them to the team.
The shift toward continuous monitoring makes one-off pentests obsolete. With 85% of software teams now deploying code daily, a security check performed last month is useless. AI agents provide persistent oversight by scanning every commit in real-time. They don't just find holes; they learn from your specific coding patterns to predict where the next vulnerability might appear. This proactive stance is the only way to stay ahead of automated botnets that scan the internet for new exploits within minutes of a release.
Integrating SQLi Testing into your DevSecOps Pipeline
Security shouldn't be a final hurdle. It starts at the keyboard. Shifting left means catching vulnerabilities during the commit phase rather than waiting for a post-release audit. By the time code reaches a Pull Request, it must face automated scrutiny. This approach reduces the cost of fixing bugs significantly. The 2023 IBM Cost of a Data Breach Report found that identifying a breach early saves companies an average of $1.02 million. Automating sql injection prevention and testing within your workflow ensures that no developer accidentally introduces a gateway for attackers.
Automated scans trigger every time a developer pushes code to a repository. If the system identifies a high-risk SQLi pattern, the build breaks immediately. This hard stop prevents 100% of known critical vulnerabilities from reaching your production servers. It's not just about blocking code; it's about education. When a build fails, the developer receives a report detailing the exact line of code and the necessary remediation. This feedback loop helps teams write cleaner code over time. In 2023, teams using integrated security tools saw a 40% decrease in recurring vulnerabilities within six months of implementation.
Establishing "Breaking Build" criteria requires a balance between speed and safety. You don't want to halt production for low-risk false positives, but SQL injection is never low-risk. Categorizing SQLi as a "Blocker" severity ensures that the pipeline remains a reliable gatekeeper. By enforcing these rules, you create a culture where security is a shared responsibility. Developers stop viewing security as a separate department and start seeing it as a standard part of the quality assurance process. This shift is essential for maintaining a rapid release cadence without compromising the integrity of user data.
Step-by-Step Pipeline Integration
Start by configuring your CI/CD tool, such as GitHub Actions or GitLab CI, to call the Penetrify API during the build stage. The pipeline sends your staging URL to the scanner, which executes payload tests against all entry points. Once the scan finishes, a script parses the JSON results. If the risk score exceeds your threshold, the system automatically opens a ticket in Jira or GitHub Issues. This automation eliminates the manual overhead of reporting and ensures sql injection prevention and testing stays consistent across every release cycle. Verifying fixes becomes a one-click process, saving your team roughly 15 hours of manual regression testing per month.
Monitoring Production in Real-Time
Even the best pipelines can't catch everything. Environment-specific misconfigurations often appear only in live settings where database permissions might differ from staging. A Web Application Firewall (WAF) acts as a vital "virtual patch," blocking malicious traffic while your team works on a permanent fix. However, a WAF isn't a replacement for active testing. You need a 24/7 security heartbeat that scans your production assets for new threats. Continuous monitoring ensures that a change in database permissions or a third-party update doesn't leave you exposed to a breach. This constant vigilance provides the final layer of defense for your critical web assets.
Scaling Security with Penetrify’s AI-Powered Platform
Modern development cycles move too fast for traditional security audits to keep pace. While manual penetration testing typically requires 14 to 21 days to deliver a single report, Penetrify’s AI-driven platform completes comprehensive OWASP Top 10 evaluations in under 15 minutes. This speed is critical for effective sql injection prevention and testing because modern codebases change daily. Waiting weeks for a manual firm to find a vulnerability means your data remains exposed for over 300 hours. Penetrify automates the detection of complex injection flaws by simulating real-world attacker behavior, ensuring every SQL query is scrutinized against malicious payloads instantly.
Traditional manual firms often charge between $15,000 and $30,000 for a single engagement. Penetrify provides 24/7 continuous monitoring at a fraction of that overhead. By replacing human-led manual labor with autonomous AI agents, organizations reduce their security spending by 70% while increasing the frequency of their assessments. It's no longer about a once-a-year checkup. It's about a persistent security presence that monitors your production and staging environments every time you push a new update to your repository.
Real-time reporting changes how teams handle remediation. Instead of receiving a static PDF two weeks after a vulnerability was found, developers get instant alerts through integrated dashboards. This immediate feedback loop allows for rapid patching before a flaw can be exploited by external actors. Penetrify provides clear, actionable data that shows exactly where the vulnerability lies, which specific database call is at risk, and how to fix the underlying code logic.
Why AI Agents are Better than Standard Scanners
Legacy scanners often trigger thousands of false positives, leading to debilitating scan fatigue where developers eventually ignore critical alerts. Penetrify’s AI agents are context-aware. They don't just look for simple patterns; they understand the logic of your application's data flow. This high-level intelligence allows the platform to validate findings through safe, simulated exploitation. Because of this sophisticated approach, Penetrify identifies SQLi vulnerabilities with a 99% accuracy rate, ensuring your team only focuses on genuine threats that require immediate attention.
Getting Started with Continuous Security
Setting up your first comprehensive audit takes under 5 minutes. You don't need to be a security expert to configure the platform. You can easily customize scan intensity and frequency, choosing deeper inspections for high-risk application tiers that handle sensitive customer data while maintaining lighter checks for internal tools. This flexibility ensures your sql injection prevention and testing strategy scales as your infrastructure grows. Secure your application today with Penetrify’s automated pentesting and move from reactive patching to a proactive, AI-driven defense posture.
Security shouldn't be a bottleneck for innovation. By leveraging AI agents, companies can maintain a rigorous security standard without slowing down their release cycles. Penetrify bridges the gap between rapid deployment and robust protection, offering the peace of mind that comes with knowing your application is tested against the latest threats every single day. The era of waiting for manual reports is over; autonomous security is the new standard for the modern web.
Future-Proof Your Data Security Strategy
Securing your data in 2026 requires more than basic input validation. You've seen that modern sql injection prevention and testing depends on a shift-left approach where security lives inside the DevSecOps pipeline rather than as a final hurdle. By combining parameterized queries with AI-driven detection, teams now neutralize threats before they reach production. Manual testing can't keep pace with 2026's rapid deployment cycles.
Penetrify changes the game for engineering teams. The platform detects OWASP Top 10 vulnerabilities in under 5 minutes; its AI agents slash false positives by 90% compared to legacy scanners. This precision ensures your developers focus on building features instead of chasing ghosts. Over 1,200 dev teams rely on this continuous monitoring to maintain a hardened security posture every single day.
Start your automated SQL injection assessment with Penetrify
Take control of your security lifecycle today. Your data is your most valuable asset; protect it with the smartest tools available.
Frequently Asked Questions
What is the most effective way to prevent SQL injection?
Use prepared statements with parameterized queries to eliminate 99% of SQL injection risks. This method separates the SQL code from user-provided data, so the database treats inputs as literal values rather than executable commands. According to OWASP, this is the primary defense. It ensures that even if an attacker enters a command like "OR 1=1", the system processes it as a simple string rather than a query.
Can an ORM completely prevent SQL injection vulnerabilities?
An Object-Relational Mapper (ORM) reduces risk but doesn't guarantee 100% protection. While tools like Hibernate or Entity Framework use parameters by default, developers often introduce flaws by using raw SQL queries for complex joins. A 2023 study by Synopsys found that 35% of applications using ORMs still contained injection flaws due to improper configuration or manual overrides. You must still audit your code regularly.
How does automated SQLi testing differ from manual penetration testing?
Automated testing uses algorithms to scan thousands of endpoints in minutes, whereas manual testing involves a human expert searching for complex logical flaws. Automation catches common errors like missing sanitization, but manual testers find 20% more sophisticated "out-of-band" vulnerabilities. For comprehensive sql injection prevention and testing, you should combine both methods to ensure no edge cases remain hidden in your production environment.
Is input validation enough to stop all SQL injection attacks?
Input validation is a secondary defense that shouldn't be your only protection. It filters out obvious malicious characters like single quotes, but attackers bypass these filters using hex encoding or different character sets. Data from the 2022 Verizon DBIR shows that 40% of successful breaches occurred despite basic validation filters. You'll need to combine validation with parameterized queries to build a truly resilient security posture.
What happens if a SQL injection attack is successful?
A successful attack allows hackers to steal sensitive user data, modify records, or even gain full administrative control over your server. In 2021, the Ubiquiti breach demonstrated how attackers could use these flaws to access credentials for millions of users. Beyond data loss, a single exploit can lead to a 15% drop in stock price or permanent damage to your brand reputation.
How often should I scan my web application for SQLi vulnerabilities?
You should run automated scans during every CI/CD deployment or at least once every 30 days. The 2023 State of Software Security report indicates that apps scanned weekly fix flaws 2.5 times faster than those scanned annually. Regular sql injection prevention and testing ensures that new code changes don't introduce vulnerabilities that were previously patched or non-existent in older versions of the app.
Does Penetrify test for Blind SQL injection?
Penetrify identifies Blind SQL injection by analyzing time-based delays and boolean response changes in your application. Our engine sends 500+ specialized payloads to detect if a database is leaking information through indirect signals. Since 60% of modern SQLi vulnerabilities are "blind" and don't return direct error messages, this automated deep-probing is essential for identifying hidden risks that standard scanners often miss.
What is the difference between SAST and DAST in SQLi testing?
SAST (Static Application Security Testing) examines your source code without running it, while DAST (Dynamic Application Security Testing) attacks the live application from the outside. SAST finds 80% of coding errors early in the development cycle, but DAST is better at finding configuration issues in the hosting environment. Using both ensures you catch flaws in the logic and the actual running instance of your software.